Fortinet Review: Quick Expert Summary
While Fortinet has some really good security features, it’s intended for enterprise users rather than home users. This review explores the viability of Fortinet from a home user perspective, but home users should check out these better options first:
🥇1. Norton — Norton is the best overall antivirus in 2024. It has a powerful malware engine that uses machine learning and advanced heuristics, plus tons of additional features — including a firewall, web protection, password manager, and more.
🥈2. Bitdefender — Bitdefender is an excellent antivirus that uses a cloud-based engine to protect your computer without using many resources. It also includes advanced ransomware protection, good system optimization tools, parental controls, and more.
🥉3. McAfee — McAfee is a really good program with great web protection. It’s also one of the most feature-rich antiviruses on the market, including a firewall, anti-phishing protection, identity theft protection, and more.
Fortinet is a powerful antivirus and security suite for business and enterprise users. It comes with excellent features to protect up to 10,000 endpoints, which include:
- Antivirus scanner.
- Vulnerability scanner.
- Firewall.
- Sandbox.
- And more…
Fortinet’s features can be accessed and initiated remotely from Fortinet’s Endpoint Management System (EMS). This intuitive web-based dashboard gives administrators complete control over endpoints on their network. It works really well and is super easy to navigate.
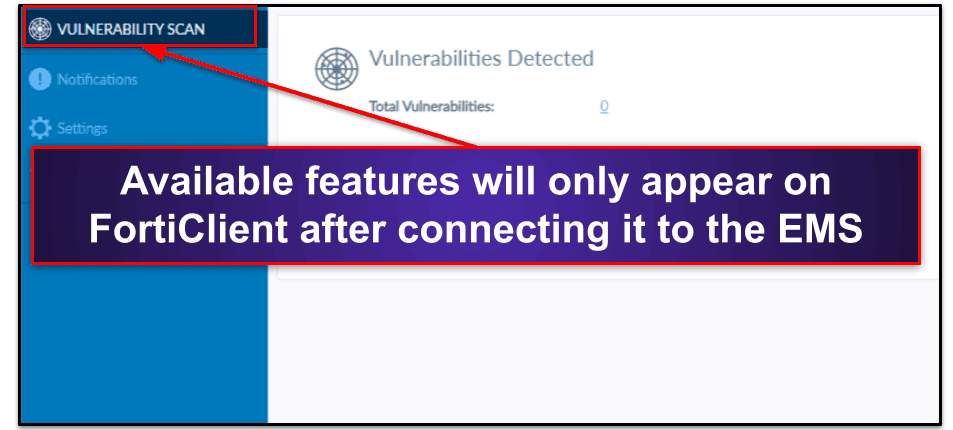
However, you can only access Fortinet’s features if you connect FortiClient (the individual app) to the EMS. With this in mind, home users can connect up to 3 devices to the EMS using Fortinet’s free trial — but if you’re a home user, you’re still better off choosing an alternative antivirus, since this involves a complicated setup process where you need to run your own SQL server.
Overall, I found that FortiClient isn’t a good solution for home users. It’s got excellent malware protection, a powerful firewall, and it’s really easy to use, but it was developed for business users. Home user are better off choosing an alternative antivirus like Norton that doesn’t require a server to constantly run in the background.
| Overall Rank | #41 out of 74 antiviruses |
| 🔥 Firewall | ✅ |
| 🌐 VPN | SSL/IPsec Only |
| 🎁 Free Plan | ❌
(but there is an unlimited free trial that can protect up to 3 devices) |
| 💵 Pricing | Request a quote with a Fortinet Partner |
| 💰 Money-Back Guarantee | ❌ |
| 💻 Operating Systems | Windows, Mac, iOS, Android, Chromebook, Linux |
Fortinet Full Review
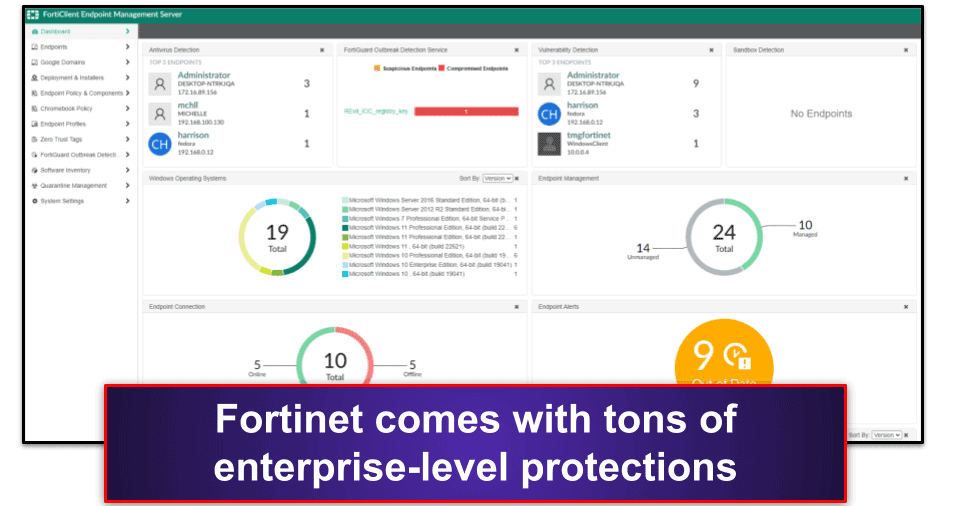
Fortinet is an excellent security suite for enterprise and business users. It includes good malware protection, an in-depth vulnerability scanner, and a powerful web filter.
However, none of Fortinet’s features work if FortiClient isn’t connected to the EMS — which is really disappointing. For that reason, Fortinet’s not a viable solution for home users because the premium plans have a high-entry point (starting at ), and the 3-user free trial involves a complicated setup process.
Home users should instead pick an antivirus from our list of the top 10 best antiviruses.
Fortinet Security Features
Antivirus Scan
Fortinet’s malware scanner scans for and removes malware in system files, applications, removable media, drivers, and dynamic-link library (DLL) files. There’s a wide range of scanning options, which can all be run on demand from the endpoint or launched remotely from the endpoint management system (EMS), including:
- Quick Scan — Scans for rootkits and malware in running applications.
- Full Scan — Scans every file and folder on an endpoint for malware and rootkits.
- Custom Scan — Lets you pick specific files or folders and scan them for malware or rootkits.
- Removable Media Scan — Scans for and removes malware and rootkits from removable media.
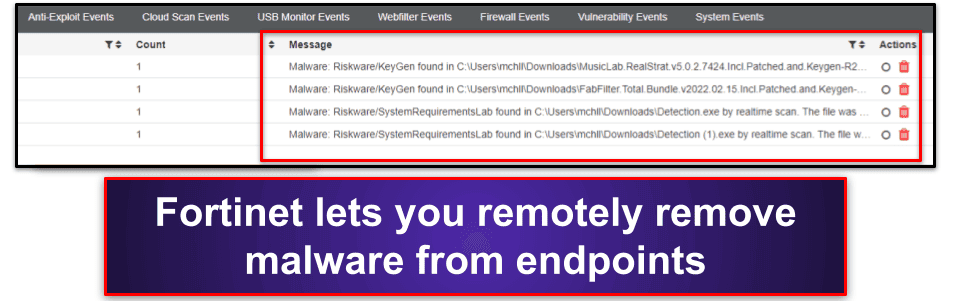
I really like how you can run these scans from the EMS. It makes it easy to quickly look for malware on multiple machines without having to access them. I also like how Fortinet’s EMS lets you see each machine’s quarantine folder. You can go into any scanned computer from the EMS and quickly clear out its quarantine list.
The only downside is that FortiClient needs to be connected to the EMS before you run the malware scanner — which makes little sense since older versions of FortiClient let you run malware scans without relying on the EMS. Many competitors can be run on individual machines without being connected to a management console.
Overall, Fortinet provides excellent scanning options, but home users won’t be able to use it without connecting it to the EMS first. On the other hand, business users will find it easy to run malware scans on all endpoints from one intuitive dashboard.
Vulnerability Scan
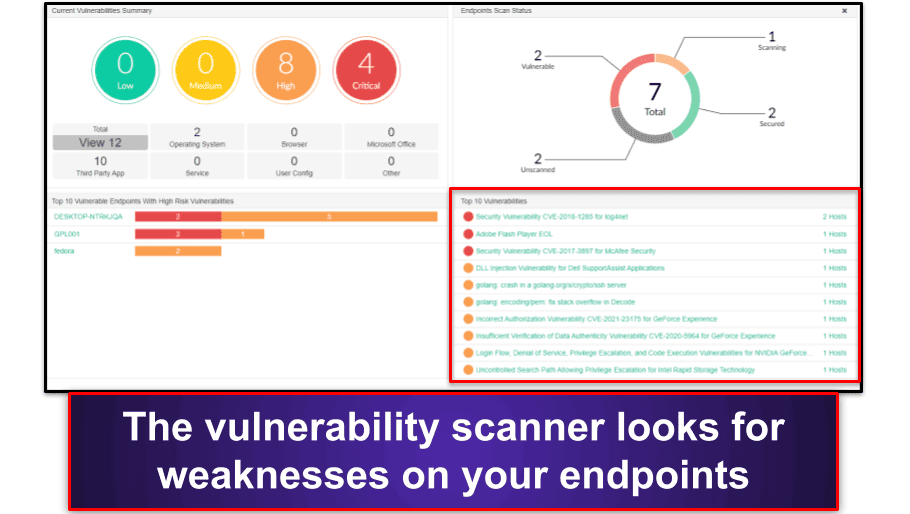
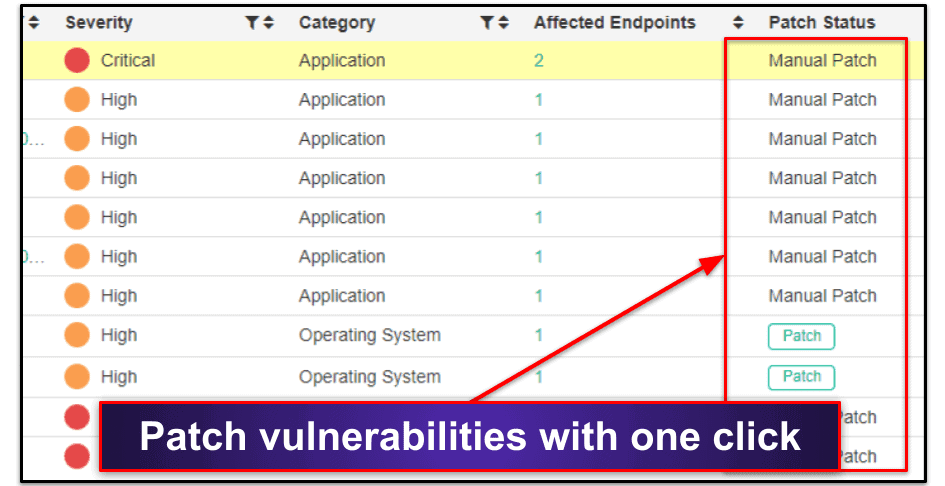
Fortinet’s vulnerability scanner looks for known weaknesses on your endpoints and helps you to patch them. For example, Fortinet can scan for applications at risk of DLL injection, DOS attacks, and more.
If Fortinet finds a vulnerability, it lists the number of endpoints affected by it. It then either lets you patch the vulnerability in one click or informs you that you need to manually patch the vulnerability from the endpoint.
You can also click on the vulnerability to learn more about it, which is pretty cool.
Like with the antivirus scanner, Fortinet also lets you run the vulnerability scanner remotely or from the endpoint — but again, the endpoint must be connected to the EMS for the vulnerability scanner to work.
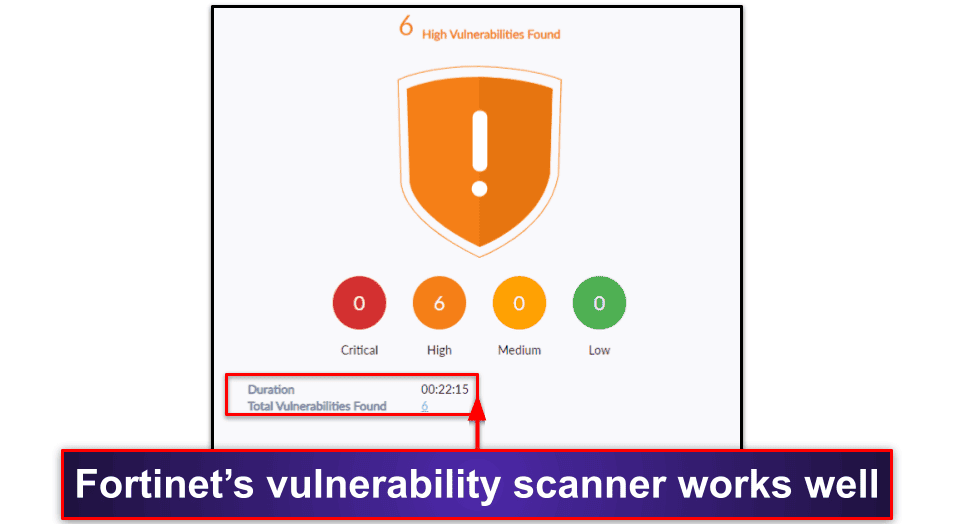
I ran the vulnerability scanner locally on my Windows 11 computer, and I was quite impressed by it. It took 22 minutes to complete and found vulnerabilities that many other antivirus programs missed.
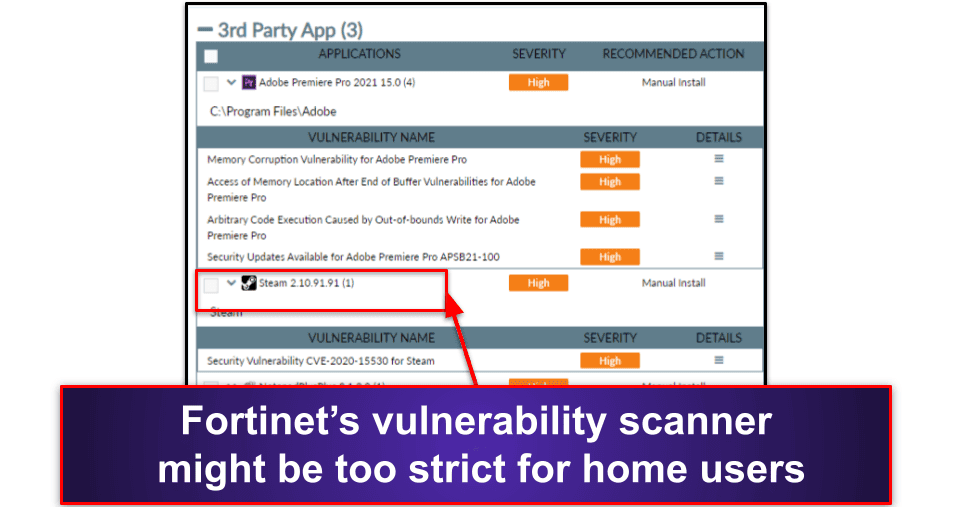
However, I do worry the vulnerability scanner is a little too strict. For example, it pointed out vulnerabilities in Steam and marked them as high severity. Steam is one of the most popular gaming apps in the world, so I’d be surprised if it had major vulnerabilities.
Overall, I really like Fortinet’s vulnerability scanner even if it is a little strict. It’s well laid out, easy to use, and makes it super easy to patch vulnerabilities.
Web Filter
Fortinet’s web filter automatically blocks malicious websites and sites you don’t want users on your endpoints visiting. It also lists every website users have accessed and allows you to turn on Safe Search for specific machines.
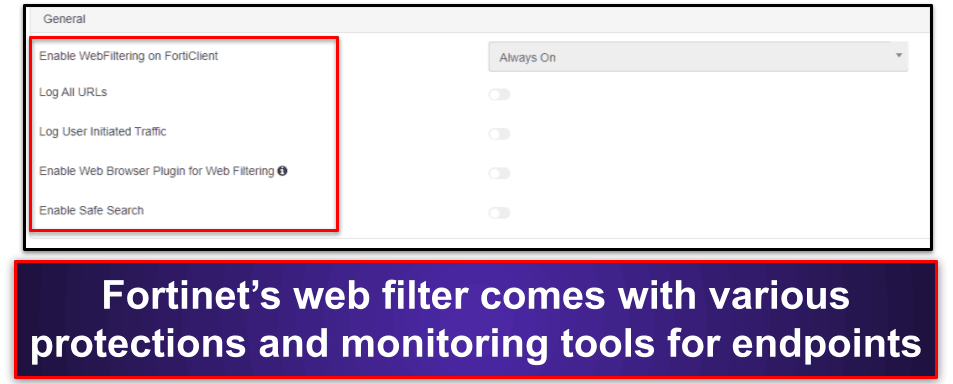
Fortinet’s automatic web filter can block websites in 87 categories, including social media, porn, and gambling. This is more categories than Norton’s parental controls, and I also like how you can set up specific profiles, so filters are only applied to specific machines in your network.
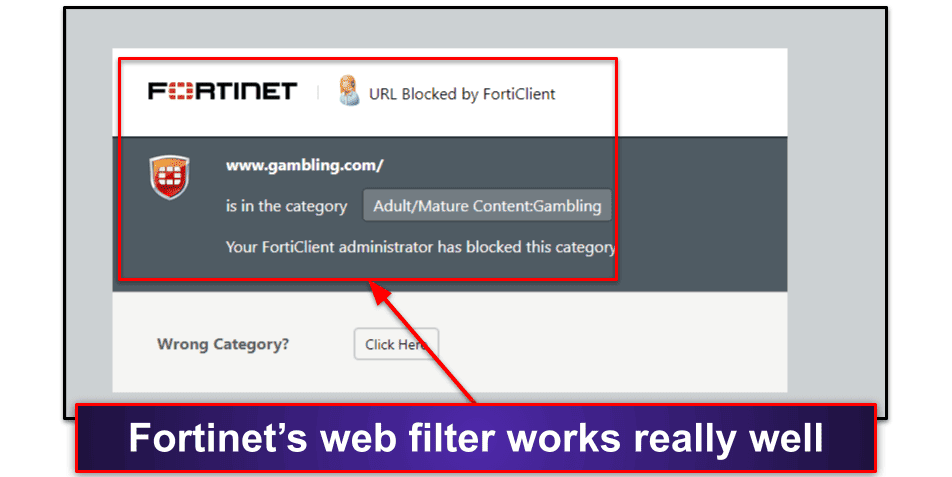
In my tests, the web filter worked really well. I couldn’t visit gambling websites on my endpoint after blocking them on the EMS. However, I found I was able to visit a lot of phishing websites that competitors like Norton and McAfee blocked.
Fortinet also allows you to issue a warning to users, so rather than blocking access to a website entirely, they have the choice to continue, but with the understanding that Fortinet will log the website on the EMS. This is a great way to prevent staff or family members from being blocked by a false positive.
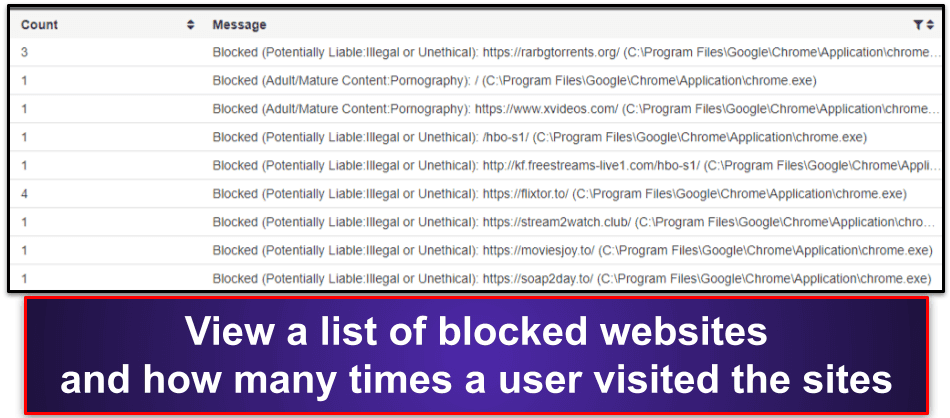
Overall, Fortinet’s web filter is pretty good. It automatically blocks malicious and inappropriate websites, allows you to create custom profiles for specific machines, and lists every website an endpoint user has tried visiting.
Firewall
Fortinet includes a signature-based firewall that scans for and blocks network-based exploits and untrustworthy applications. It works pretty well, and it blocked the majority of the simulated exploit attacks I tested against it.
Like with the web filter, you can create specific policies for individual computers. For example, you can set up Fortinet to monitor network traffic in emails for the engineering team, but not for the sales team.
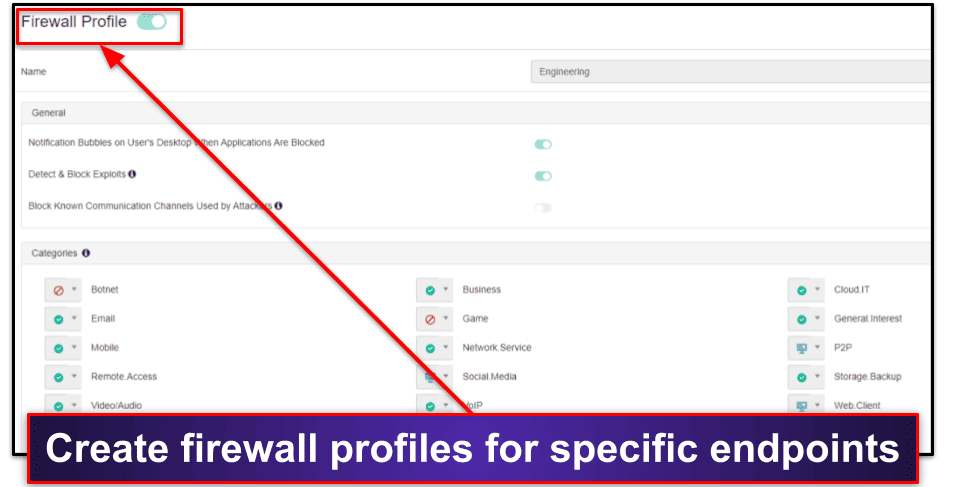
Fortinet also has several customization options, but I was surprised at some of them. For example, you can switch off Fortinet’s ability to detect and block exploits — and I don’t know why anyone would want to do that.
Finally, Fortinet lets you see all the firewall events for a particular machine and what exploits the system has blocked. This is pretty cool, but I was disappointed that the log doesn’t make it easy to whitelist false positives. When I tried clicking on a listed firewall event, it simply highlighted the event and allowed me to remove it. Competitors like ESET let you whitelist false positives in just a few clicks.
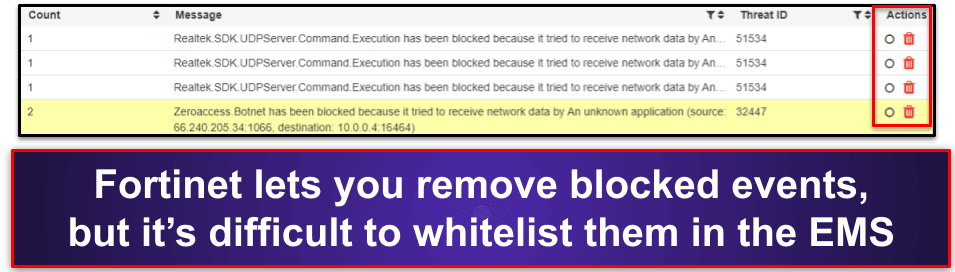
Overall, Fortinet provides a pretty good signature-based firewall that can prevent network-based attacks on machines in your network.
VPN
Fortinet’s VPN allows you to connect to an SSL or IPsec VPN. In that regard, it works a little differently than most VPNs on the market. Instead of connecting to a preconfigured server in a specific country, Fortinet’s VPN requires an enterprise firewall or FortiGate virtual machine (the virtual version of Fortinet’s physical firewall) to be running.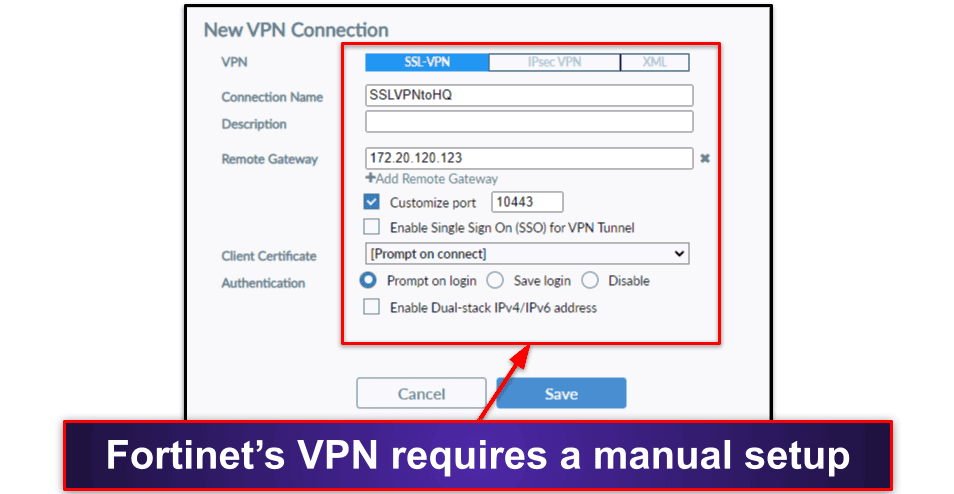
Unfortunately, this makes Fortinet’s VPN inaccessible for home users. So, if you’re a home user and want to connect to remote servers to browse the internet privately, you should choose a VPN such as ExpressVPN.
However, if you’re a business user running FortiGate or FortiGate-VM, connecting via Fortinet’s VPN comes with some advantages. For example, it gives you secure access to corporate networks, which helps prevent things like man-in-the-middle attacks.
Administrators on Fortinet’s EMS also get various controls to help secure computers connected to the VPN. For example, they can choose whether or not to allow personal VPNs on specific computers and whether or not particular profiles should use an SSL VPN DNS.
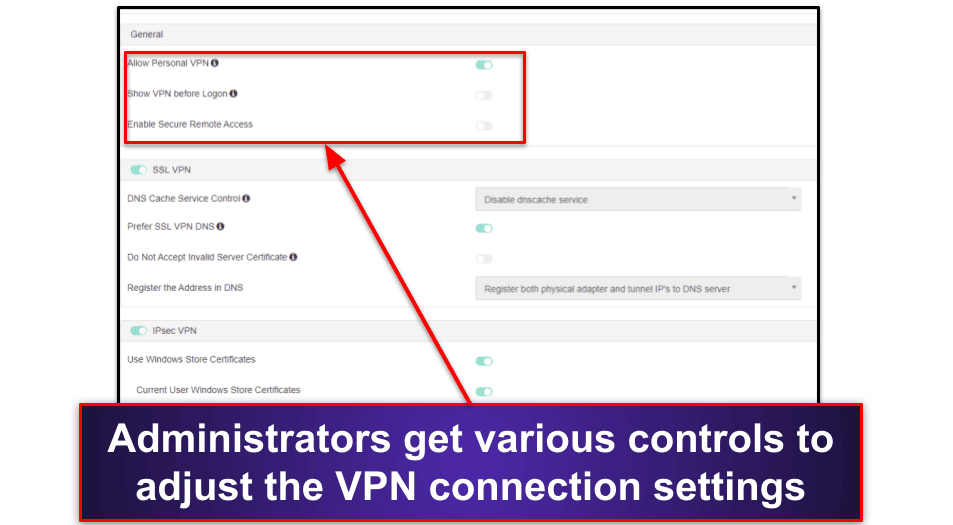
Overall, Fortinet’s VPN isn’t much more than a gateway to the FortiGate firewall. It isn’t a personal VPN like standalone brands such as ExpressVPN and Private Internet Access (PIA), so home users won’t have much use for it. That said, it’s a great way to secure business users’ access to the FortiGate Firewall.
Sandbox
FortiClient’s sandbox (FortiSandbox) uses machine learning to detect and scan suspicious files in a virtualized environment that’s isolated from your main network. It’s an excellent way for work environments to protect their networks or endpoints from dangerous email attachments, applications, and more.
However, like Fortinet’s VPN, FortiSandbox works differently than regular sandboxes. For example, Comodo’s sandbox utilizes a virtual desktop where you can access and navigate an isolated environment. But Fortinet’s sandbox runs alongside FortiGate and automatically receives files to test based on your specific settings. There’s no way for an endpoint user to open and navigate inside a virtualized environment like there is with Comodo.
Administrators on the EMS can create a basic profile that automatically sends web, email, and removable media downloads from an endpoint to the sandbox for testing. If Fortinet finds anything suspicious (such as malware), it’ll quarantine or delete the file containing malware before it can cause damage to the endpoint or network.
I really like how you can customize what’s sent to the sandbox. For example, you can choose specific file extensions that skip testing, and you can also select the remediation actions that happen if Fortinet finds suspicious files.
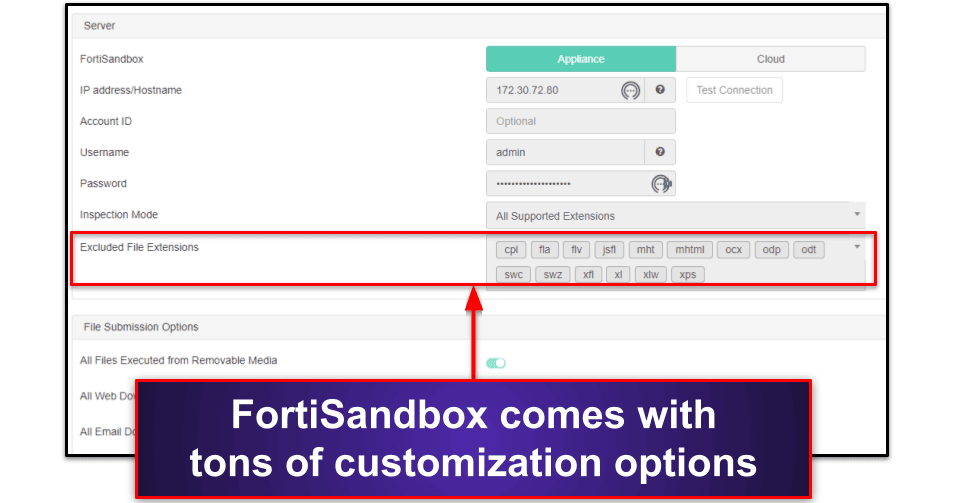
That said, home users don’t need to use FortiSandbox. While it’s great for businesses to scan and test files on multiple endpoints automatically, home users are better off choosing an antivirus with excellent real-time protection, such as Norton. However, if you’re a home user and want a virtualized environment, Comodo is also a great choice.
Additional Features
Fortinet comes with tons of additional features, such as:
- Zero trust tags — Create rules to categorize endpoints based on specific criteria. For example, you can create a rule to automatically tag all endpoints that don’t have an antivirus running, and Fortinet will group the tagged endpoints so you can easily see them.
- Outbreak detection — Alerts you to large-scale cybersecurity outbreaks. These outbreaks may not be affecting your network or endpoints, but Fortinet will inform you on how to best protect yourself from them.
- Software inventory — Shows every piece of software installed on your endpoints, which is a great way to see if any users have installed or uninstalled programs they shouldn’t have.
- Quarantine management — Lists every piece of malware found across all endpoints, the number of instances of the malware, and its status (whether or not it’s been removed).
The software inventory is a great organization tool, especially for large-scale businesses looking to control which applications are on a network. There might be some viability here for parents wanting to monitor their kids — however, parental control tools such as Qustodio also let you block unwanted apps and monitor usage time, which I think is much more useful for home users.
Overall, Fortinet has some really good monitoring features that let you see everything happening across a network of endpoints. I wish it allowed for more specific controls (for example, you can’t stop individual applications from being installed, only monitor them). However, it’s still super helpful and saves a lot of micromanagement inside a business.
Fortinet Plans & Pricing
Depending on how you want to use Fortinet, there are tons of different pricing options for enterprise and small business users — some of which include physical hardware such as FortiGate. It’s quite complicated, so Fortinet has an in-depth ordering guide.
However, to keep this review simple, I’ll focus on FortiClient and its EMS — taking Fortinet’s product and download page at face value. With that in mind, Fortinet comes with 4 different plans:
- ZTNA Edition
- EPP/APT Edition
- FortiClient EMS
- FortiClient VPN only
Whether you pick ZTNA Edition or EPP/APT Edition, you’ll download the same FortiClient installation — which won’t work without purchasing FortiClient EMS first. I don’t understand why FortiClient EMS isn’t packaged into each plan.
Here’s what you get with each version of Fortinet:
| ZTNA Edition (Requires FortiClient EMS) |
EPP/APT Edition (Requires FortiClient EMS) |
FortiClient EMS | FortiClient VPN Only | |
| Platforms | Windows, macOS, Linux, iOS, Android, Chromebook | Windows, macOS, Linux, iOS, Android, Chromebook | Windows, macOS, Linux, iOS, Android, Chromebook | Windows, macOS, Linux, iOS, Android, Chromebook |
| Price | Request a quote | Request a quote | Request a quote | Request a quote |
| Number of device licenses | 25-10,000 | 25-10,000 | 25-10,000 | 25-10,000 (depending on FortiClient license) |
| Malware scanning & removal | ❌ | ✅ | With EPP APT Edition | ❌ |
| Vulnerability scanner | ✅ | ✅ | With ZTNA Edition & EPP/APT Edition | ❌ |
| Web filter | ✅ | ✅ | With ZTNA Edition & EPP/APT Edition | ❌ |
| Firewall | ✅ | ✅ | With ZTNA Edition & EPP/APT Edition | ❌ |
| Sandbox | ✅ | ✅ | With ZTNA Edition & EPP/APT Edition | ❌ |
| Centralized management | ❌ (Requires FortiClient EMS) |
❌ (Requires FortiClient EMS) |
✅ | ❌ |
| VPN | ✅ | ✅ | With ZTNA Edition, EPP/APT Edition, and FortiClient VPN only | ✅ |
| Zero trust agent | ✅ | ✅ | With ZTNA Edition & EPP/APT Edition | ❌ |
| Software inventory | ✅ | ✅ | With ZTNA Edition & EPP/APT Edition | ❌ |
| Quarantine management | ✅ | ✅ | With ZTNA Edition & EPP/APT Edition | ❌ |
| SSL Inspection | ❌ | ✅ | With EPP APT Edition | ❌ |
| DNS security | ❌ | ✅ | With EPP APT Edition | ❌ |
| USB device control | ❌ | ✅ | With EPP APT Edition | ❌ |
| Customer support | ✅ | ✅ | With ZTNA Edition & EPP/APT Edition | ❌ |
ZTNA Edition
ZTNA Edition is Fortinet’s starting plan, and while this plan includes some pretty decent features like the vulnerability scanner and zero trust agent, it’s disappointing that it doesn’t have Fortinet’s in-line antivirus & anti-malware protection.
It’s also disappointing that this plan requires FortiClient’s EMS to function. Fortinet lets you download the FortiClient application for free, but it doesn’t let you run features like the vulnerability scan unless you connect it to the EMS first — which requires you purchase an additional plan. Previous versions of FortiClient let you run features independent of the EMS.
Overall, ZTNA Edition is a good starting point for businesses without a large budget, but it doesn’t include malware protection. That said, you can choose the ZTNA Edition and install an antivirus with unlimited device coverage alongside it (such as McAfee). If you do, Fortinet will recognize you have malware protection enabled via a third-party app. The only difference here is you won’t be able to run a malware scan remotely.
Fortinet offers an unlimited free trial of ZTNA Edition, which lets you protect up to 3 devices indefinitely. If you want more licenses, you need to get in touch with your local Fortinet partner, and they’ll give you a specialized quote depending on your needs.
EPP/APT Edition
EPP/APT Edition adds the malware scanner, SSL inspection, DNS security, USB device control, and more.
However, like with the ZTNA Edition, this edition won’t work without buying the FortClient EMS. In fact, I downloaded both ZTNA and EPP/APT Editions, and I was surprised that both editions installed the same version of FortiClient on my system. The differences between the two versions only become apparent when you connect FortiClient to the EMS.
Unfortunately, Fortinet doesn’t offer a money-back guarantee, and the free trial only supports the ZTNA Edition. However, if you’re running a small or large business, EPP/APT Edition is a good way to secure your endpoints with solid malware protection. You can find out more (including the cost of this plan) by contact your local Fortinet partner.
FortiClient Endpoint Management Server (EMS)
FortiClient’s EMS adds the centralized management that ZTNA and EPP/APT require to run. The EMS is easy to navigate through an intuitive web-based dashboard, supports up to 10,000 endpoint licenses, and can deploy the EPP/APT and ZTNA editions of FortiClient.
Honestly, there isn’t much else to say about this plan. Its main aim is to provide visibility and management for the ZTNA and EPP/APT editions — so I’m a little surprised it isn’t included in a packaged deal with them. However, you can try FortiClient’s EMS by getting in touch with your local Fortinet partner, or test it using a free demo online.
FortiClient VPN Only
FortiClient’s VPN includes the SSL and IPSec VPN and nothing else. This is the only plan that doesn’t require Fortinet’s EMS to work, but it does require FortiGate hardware or a FortiGate-VM. This plan is for businesses that want to protect their network from web-based intrusions.
However, I’m disappointed this plan lacks customer support. Many competitor antiviruses provide customer support on their free plans, and given that FortiClient’s VPN requires connecting with a partner and getting a specialized quote, I’d expect Fortinet to offer customer support with it.
Fortinet Ease of Use & Setup
Setting up Fortinet is pretty straightforward. First, you need to download the EMS and run it. At the login screen, enter “admin” as the username and leave the password field blank. Click Sign in, and you’ll be prompted to create a password. Once you have, click Submit.
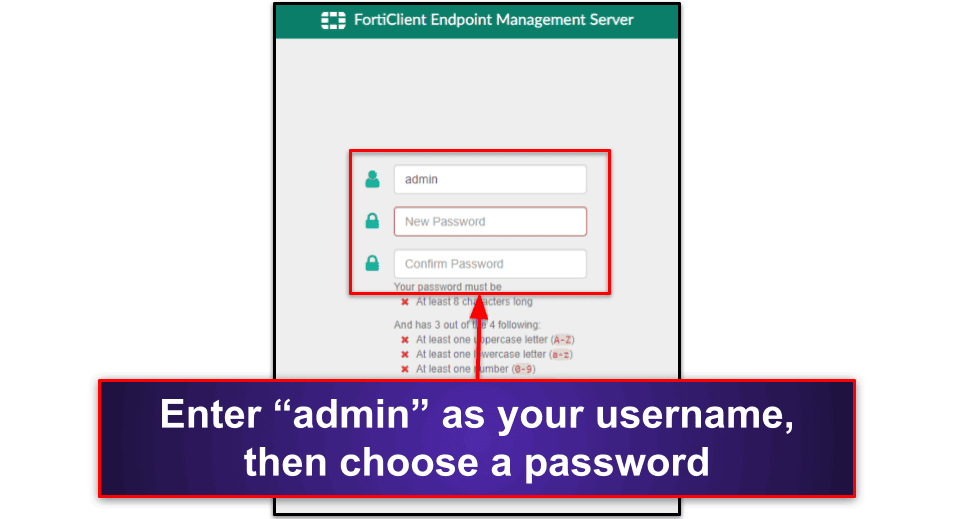
You’ll then be prompted to log into your FortiCloud account. If you haven’t got a FortiCloud account, you can sign up for one on this screen. You’ll use FortiCloud to either activate your free trial or your paid license.
You can now download FortiClient individually on each endpoint, follow the installation wizard, and connect it to the EMS using a server address/invitation code, or you can create a deployment package remotely for all of your endpoints via the EMS.
Once FortiClient has successfully connected to the endpoint, all available features will appear on the FortiClient UI (for example, when I connected FortiClient ZTNA Edition to the EMS, the vulnerability scanner appeared).
Once you’ve connected your endpoints, the EMS features an overview screen where you can see all of the most important information:
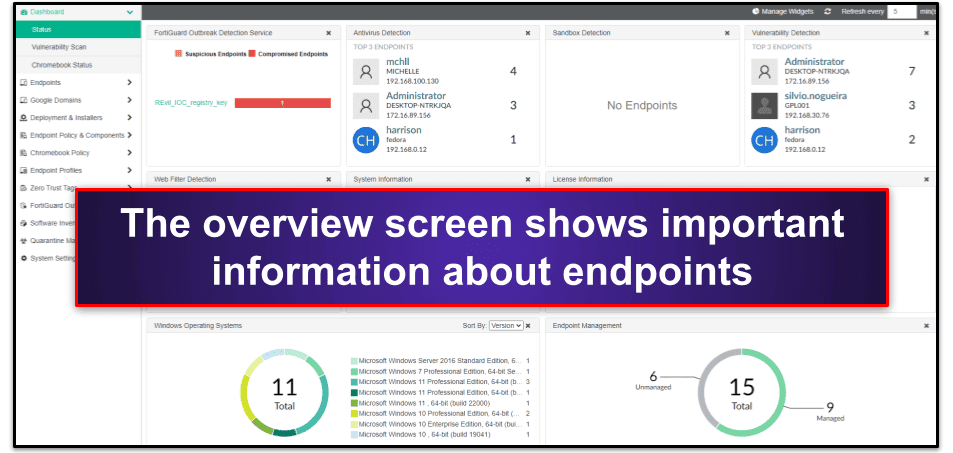
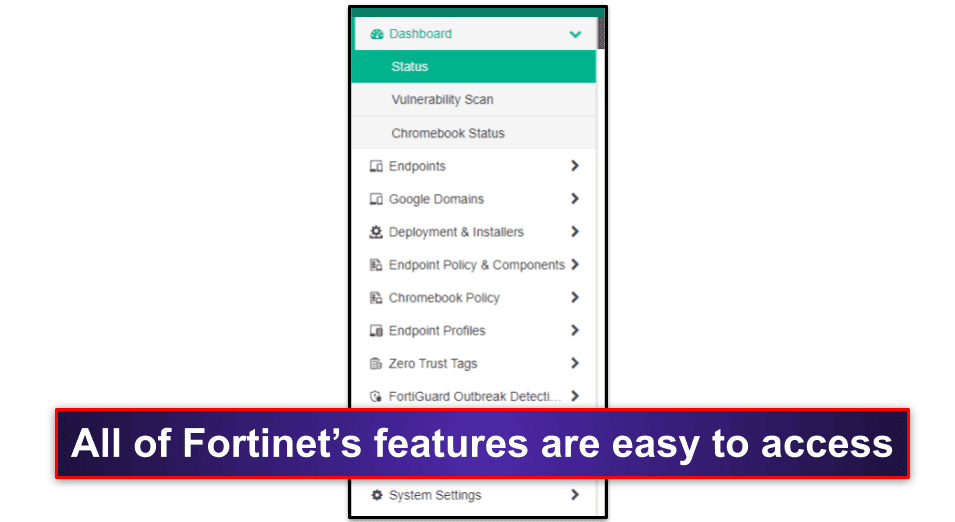
You can access all of the EMS’s features with just a few clicks using the navigation menu on the left side of the screen.
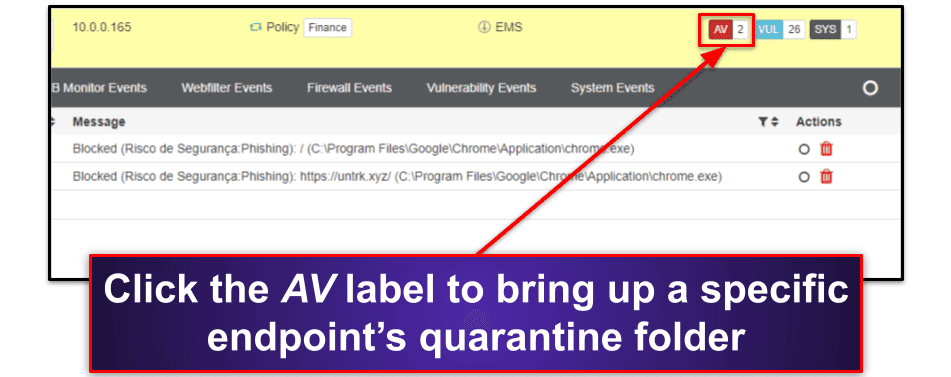
If you click Endpoints, All Endpoints, you can see the latest events for every endpoint on your network. This menu is well laid out, with important events highlighted on the right-most part of the screen.
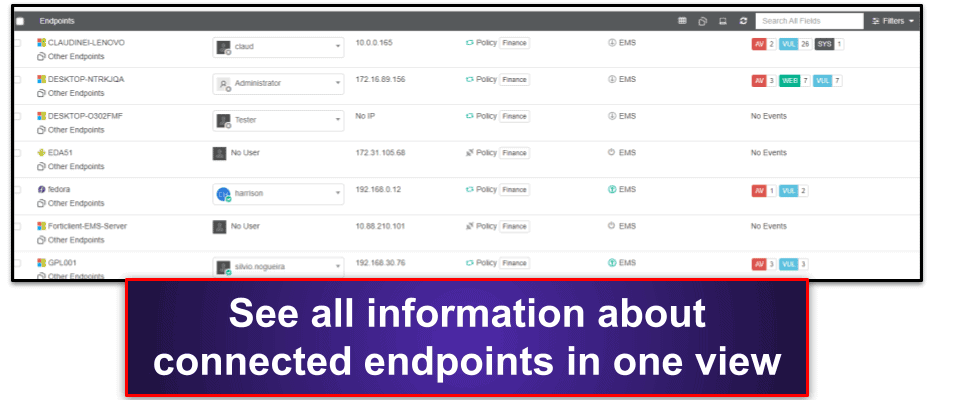
For example, the red AV label in the image above means there’s an antivirus detection, and the blue VUL label means there’s a vulnerability detection. You can click on the label to get more information about that specific endpoint — in this case, clicking the AV label brings up the endpoint’s quarantine folder.
Fortinet’s mobile app for iOS and Android works similarly to FortiClient for desktop. Most controls are accessed via the EMS (or the FortiClient mobile app when the EMS is connected).
Unfortunately, you can’t do much on Fortinet’s mobile app without connecting it to the EMS first. That said, if the mobile app is connected, administrators can initiate remote malware and vulnerability scans of your mobile device from the web. If they find any malware (or other issues), it’ll be registered on the EMS just like the desktop version of FortiClient, and administrators will be able to patch or remove it.
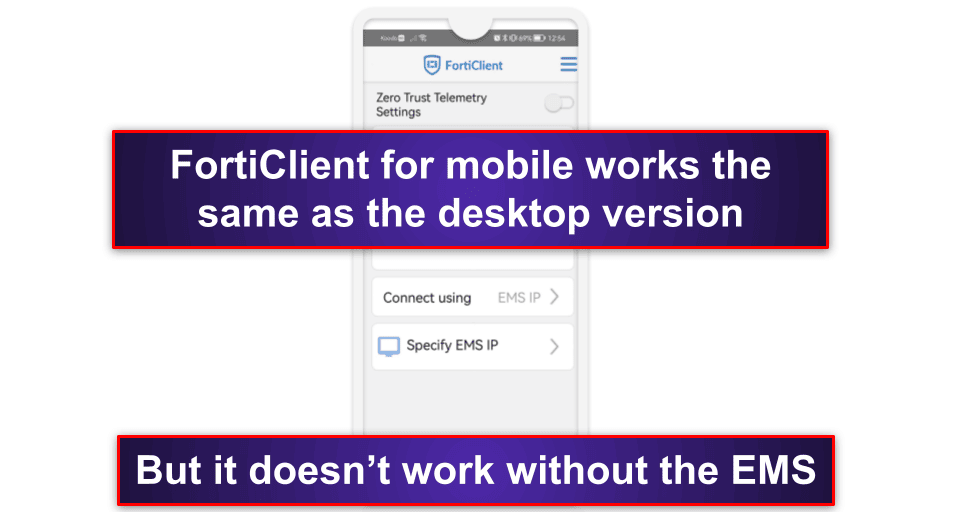
I like how the mobile app provides quick access to your phone’s settings. However, if you’re a home user, you’re better off choosing one of the best antiviruses for Android or iOS. They all provide more features for an individual and don’t require a connection to an EMS to function.
Overall, I never had any difficulty navigating Fortinet’s EMS or using its mobile app. It’s well-designed, responsive, and easy to use.
Fortinet Customer Support
Fortinet offers live chat and phone support for product registration, account management, contracts, and licensing. It has phone numbers in over 50 countries, which is impressive. Not even Norton offers customer support in that many countries.
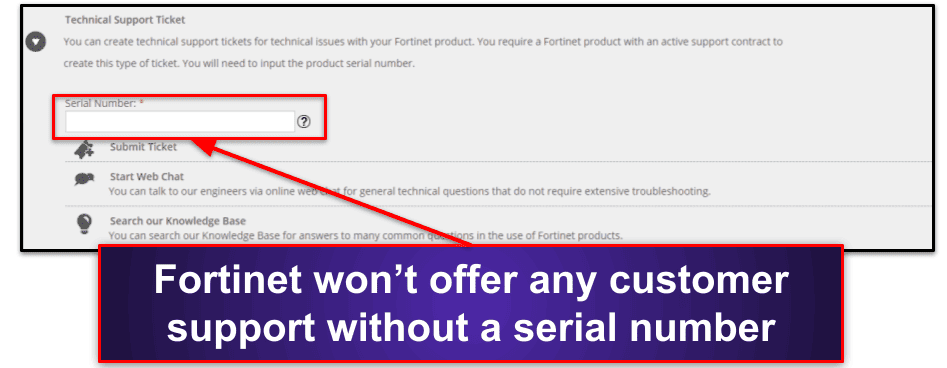
To get technical support, you have to create a free account first. Once registered, you can submit a ticket or start chatting with Fortinet’s customer service agents.
I wasn’t impressed with either of these support options. Fortinet will only help you if you provide them with a serial number and prove you’re using a paid version of the software. Many competitors, such as Bitdefender, let you contact live chat support over the phone or email without purchasing any software or giving away any details.
When I eventually managed to email Fortinet, they took 2 days to respond. In comparison, when I emailed Norton, its email support team replied in a few hours.
That being said, Fortinet does provide one of the best knowledge bases I’ve used. Each of the security applications comes with thorough guides, and I like how you can search for technical tips, solutions, and common troubleshooting issues with just a few clicks. You can also get answers for older product versions, which is cool.
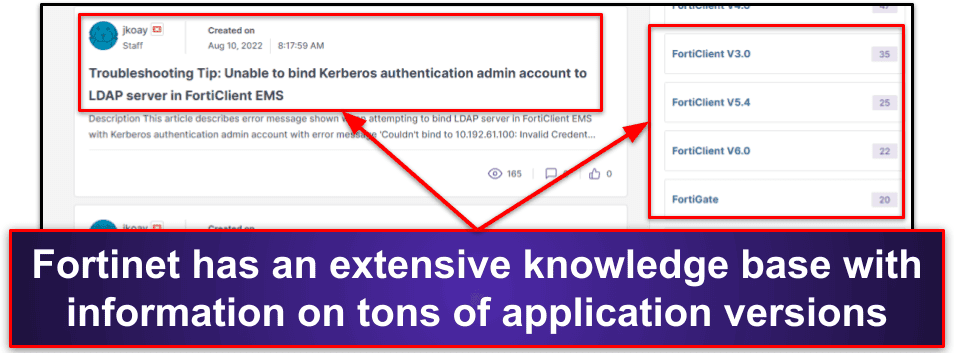
Fortinet supplies technical manuals and instructions for all of its products, which is extremely beneficial and negated the need to use any individualized support channels.
Overall, Fortinet doesn’t have great personalized support, but it has an excellent array of documentation, troubleshooting tips, and technical guides. This means you don’t need to contact customer support often anyway.
Is Fortinet Good for Home Users?
Unfortunately, Fortinet isn’t good for home users. It isn’t built with home users in mind; therefore, it’s only available at a high entry point with features intended for business users. Fortinet does offer a free trial for up to 3 endpoint licenses, but it has a complicated setup process — so most users are better off choosing an alternative antivirus meant for home use.
That said, if you’re running a business, Fortinet is a good way to protect all of your endpoints. It has many features, including an in-line malware scanner, vulnerability scanner, firewall, web filter, and more. It’s also straightforward to use. The web-based EMS dashboard provides high visibility for all of the endpoints in your network and makes running remote scans easy.
Fortinet’s mobile app is pretty good, but you need to be connected to the EMS for it to work. If you are connected to Fortinet’s EMS, you get the same features as the desktop version — depending on whether you’re using ZTNA or EPP/APT edition. For example, if you’re using the EPP/APT edition, you get malware and vulnerability scans, but if you’re using the ZTNA edition, you just get vulnerability scans.
Overall, Fortinet is good for business and enterprise users — but not for home users. It has various features to protect up to 10,000 endpoints, and it’s really easy to use. But home users are better off picking another antivirus from our top 10 list.
Frequently Asked Questions
How does Fortinet antivirus work?
Fortinet’s antivirus works like most antiviruses on the market. It scans your computer or endpoints for malware. However, FortiClient needs to be connected to Fortinet’s EMS via an invite code or URL before Fortinet’s antivirus scanner can work.
Connecting Fortinet’s antivirus to the EMS comes with several advantages. For example, it allows you to remotely initiate malware scans on your endpoints from Fortinet’s web-based dashboard.
However, for home users, there are more viable options for scanning your computer. If you’re a home user, you’re better off choosing one of the antiviruses from our list of top 10 antiviruses, which all provide excellent malware protection. I really like Norton, which includes a malware scanner, firewall, web protection, and more. You can read our full review here.
How does Fortinet’s firewall work?
Fortinet’s built-in application firewall works by scanning for and blocking network-based intrusions, including exploit-based attacks. However, like with the antivirus scanner, it won’t function unless the user is connected to Fortinet’s EMS — so it’s not viable for home users.
Fortinet also provides an additional firewall that uses machine learning to secure larger networks, but it requires physical FortiGate hardware or a FortiGate virtual machine to operate. Again, this might be a little too much for home users, but for small businesses, it offers really good security.
If you’re a home user looking for a decent firewall, you should consider Norton, which provides a really good firewall that can protect you in 2024. Bitdefender also comes with a firewall that is both highly customizable and easy to use.
Are Fortinet and FortiClient the same?
No, Fortinet and FortiClient are not the same. Fortinet is the company name, and it provides several different solutions:
- Fortinet Endpoint Management Server (EMS) — This is the web-based dashboard used to control all endpoints.
- FortiClient — This is the individual piece of software that’s installed on your Windows, Mac, Chromebook, iOS, Android, or Linux device. It will not operate without connecting it to the Fortinet EMS first.
- FortiGate — This is Fortinet’s firewall, and it’s available as physical hardware or a virtual machine (also known as FortiGate-VM).
To get Fortinet fully functioning across your network, you will need to do your research and pick the right products. However, home users are better off sticking to one of the antiviruses on our top 10 list.
Is FortiClient a good antivirus?
FortiClient is a good antivirus, but only for business or enterprise users. Home users will find they’re paying for an overpowered solution that they don’t need.
If you want to protect your entire household, you’re much better off picking an antivirus with a good family plan — like Norton 360 Deluxe, which offers coverage on up to 5 devices. This is especially important when you consider Fortinet’s licenses start at a 25-device minimum, which is quite a lot for one household. That said, if you want to cover more than 5 devices, you should check out McAfee before considering Fortinet, as it offers unlimited device coverage.

