I have trouble picking between WireGuard and OpenVPN protocols. They’re both very secure and provide great privacy, but they still each have their pros and cons, and each one is best suited for certain tasks.
So, I compared each protocol through a series of tests and did a lot of research. I ran numerous speed tests with each protocol and also checked what kind of built-in support both protocols get from the top VPNs on the market.
Overall, I think WireGuard is better than OpenVPN — it has significantly faster speeds, it’s much easier to audit, it resists network changes, and it consumes less phone battery and mobile data. I think it’s best to use WireGuard for most online activities, like browsing, streaming, torrenting, and gaming (especially when you’re using your mobile on the go).
That said, OpenVPN is still the better option for users dealing with web restrictions. Unlike WireGuard, this protocol can use TCP port 443 and also supports obfuscation — both help it circumvent VPN blocks in restrictive countries or on restrictive networks.
Ultimately, which protocol you use is 100% up to you — just make sure you get a VPN that supports both. That way, you can easily switch between WireGuard and OpenVPN for different use cases. You can also test each protocol for different online activities to see which one provides you with the best experience. Out of all the VPNs that provide access to both protocols, my favorite one is Private Internet Access since it’s very secure, easy to use, and fast. Editors' Note: Private Internet Access and this site are in the same ownership group.
WireGuard vs. OpenVPN: Quick Overview
Editors' Note: Intego, Private Internet Access, CyberGhost and ExpressVPN are owned by Kape Technologies, our parent company
What Is OpenVPN?
OpenVPN is a VPN protocol, meaning it’s a set of rules that establish how a VPN connection happens (it mainly focuses on providing encryption). OpenVPN was first developed in 2001 by James Yonan and has since been adopted by virtually all VPN providers since it provides excellent security and privacy. OpenVPN is completely free to use since it’s open-source, which means the code is publicly available to anyone.
Here’s the best VPN with OpenVPN in 2024:
Read the full ExpressVPN review >
What Is WireGuard?
WireGuard is a VPN protocol, which means it’s responsible for how a VPN connection is established and secured. WireGuard is open-source and was developed by Jason A. Donenfeld. It was initially released in 2015 and received a stable release (when it passed all verifications and tests) in 2020. Its adoption was slow at first, but most top vendors have started offering built-in support for the protocol on most of their apps in recent years.
Here’s the best VPN with WireGuard in 2024:
Read the full Private Internet Access review >
Editors' Note: Private Internet Access and this site are in the same ownership group.
WireGuard vs. OpenVPN: Speeds
OpenVPN has good speeds, but it simply can’t keep up with WireGuard, which is designed to be lightweight and provide really fast speeds.
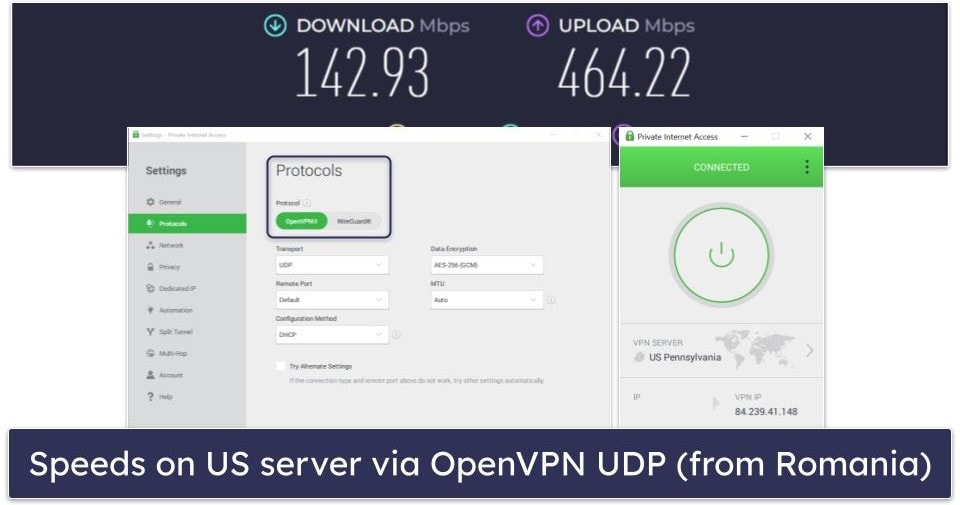
I confirmed this by running multiple speed tests with both OpenVPN and WireGuard. I used Private Internet Access (PIA) for these tests, as it has both protocols, and it’s also the second fastest VPN on the market. To keep things fair, I used OpenVPN over UDP in my tests, as UDP is much faster than TCP.
I ran speed tests with each protocol on servers in 10 countries, and I tested both nearby and distant server locations. WireGuard always provided the fastest speeds for browsing sites, watching HD videos, downloading torrents, and playing online games — with OpenVPN, I experienced minor (but still noticeable) slowdowns for the same activities while connected to distant servers.
For reference, here’s a look at what speeds I had with OpenVPN UDP on a US server:
Here are the speeds I had on the same server location when using WireGuard:

With WireGuard, my VPN speeds were around 71% faster than with OpenVPN, which is a pretty significant difference.
In addition to the tests I did while connected to PIA, I also ran similar tests with other top VPNs that use WireGuard and OpenVPN, including CyberGhost VPN, Surfshark, and Proton VPN. In all of those tests, I always maintained faster browsing, streaming, downloading, and gaming speeds with WireGuard — on both nearby and distant servers.
Winner (Speeds): WireGuard
WireGuard always performs better than OpenVPN when it comes to speeds (even if you use OpenVPN over UDP). WireGuard is designed to be very lightweight, which helps it maintain fast speeds for all online activities on both nearby and distant servers. Don’t get me wrong — OpenVPN is still pretty fast, but you’ll likely notice some slowdowns, especially on distant servers.
WireGuard vs. OpenVPN: Security
Both VPN protocols provide excellent security. Even though OpenVPN provides better flexibility since it can use more encryption options than WireGuard, this won’t be very noticeable to the VPN user.
Each ones uses very good encryption ciphers, which are used to make your data unreadable. WireGuard only uses ChaCha20, whereas OpenVPN can use ChaCha20 and many other ciphers — this includes AES (the most commonly used cipher), Camellia, and virtually any other cipher in the OpenSSL library, which OpenVPN uses to provide encryption.
Some online sources claim that WireGuard is too restrictive by only using ChaCha20, but I don’t find that to be an issue. ChaCha20 provides pretty much the same level of security as AES (which OpenVPN usually uses) — and AES is the same encryption cipher that’s used by military and financial institutions. Also, some OpenVPN support articles even recommend using ChaCha20 as an alternative to AES.
Plus, one could also argue that OpenVPN’s usage of so many ciphers makes it more complex, which increases the risk of human error when implementing it. And, it also provides a bigger attack surface that cybercriminals could try to exploit.
Other than that, both protocols use strong authentication protocols (the verification of a user or device trying to connect to a VPN). WireGuard uses Poly1305, while OpenVPN can use poly1305, CBC, GCM, ECB, and more.
WireGuard and OpenVPN also use secure hashing methods, too — hashing is used to verify the integrity of transferred data to make sure it’s not been altered. WireGuard uses BLAKE2s for hashing, while OpenVPN can use BLAKE2, SHA-1, SHA-2, SHA-3, and more.
Also, both protocols support perfect forward secrecy — this is a security method that provides a different encryption key for each VPN session. This ensures that cybercriminals can’t use past or future session keys that might be compromised to monitor your VPN connections.
Finally, neither protocol has any known security vulnerabilities. Plus, both WireGuard and OpenVPN have passed multiple security audits over the years — only minor security issues were found sometimes, and they were quickly fixed.
Winner (Security): It’s a tie
There’s really no way to pick a winner here. While OpenVPN is able to use more encryption methods than WireGuard, both protocols still use extremely secure encryption ciphers, authentication protocols, and hashing. Plus, they both support perfect forward secrecy, and neither protocol has any serious security vulnerabilities.
WireGuard vs. OpenVPN: Privacy
I honestly think that both VPN protocols provide excellent privacy — even though most online sources claim that WireGuard wasn’t designed with privacy in mind, and that it might compromise your IP address.
The main thing is that both WireGuard and OpenVPN are open-source. This means their codebase is available to the public, so anyone (who has the skills) can inspect each protocol’s code to make sure there are no privacy or security issues.
However, by default, only OpenVPN doesn’t require any type of logging. So, the VPN providers that use it don’t need to implement any changes to protect users’ privacy.
WireGuard’s default build, on the other hand, comes with some privacy concerns. Basically, the protocol can’t dynamically assign VPN IP addresses to VPN users, which would normally force VPN providers to store user IPs on their servers — and that data is only removed when the server is rebooted.
I know that sounds bad, but I honestly don’t consider it a deal-breaker since all the top VPNs that have implemented WireGuard in their apps have also taken precautions to protect users’ privacy. Here are some examples of how VPNs handle this issue:
- Double NAT (Network Address Translation) systems. Some providers use 2 network interfaces to mitigate the IP logging issue. One interface assigns a local IP to all users connected to a server, while the second interface assigns a unique IP for each VPN tunnel — this allows data to travel between VPN users and the sites they access without having to link a specific user’s identity to the assigned local IP address. NordVPN uses a Double NAT system in its NordLynx protocol, which is based on WireGuard.
- Handshake scanners. Some VPNs, like Mullvad VPN for example, use automated programs that check the handshake timestamps for their peers — basically, when a device establishes a secure connection to a VPN server. If the program detects that a handshake hasn’t taken place in a set amount of time, like 300 seconds for example, it drops and restarts the VPN session, deleting all data associated with the last handshake (including user IPs).
- Dynamic configurations. The VPN provider configures its servers to provide a unique configuration (a list of things needed for a VPN connection to run) for each VPN session. This way, when a user disconnects from the VPN server, all the data contained in the configuration, including the IPs, is deleted.
- Modified data output. Some VPNs (like Windscribe) have modified their servers to ensure they don’t output the data that contains users’ IP addresses. This way, the data is still visible to the WireGuard protocol, but not to the VPN provider.
- RAM-only servers. Many top VPNs only use VPN servers that run on RAM. This way, if any data (including user IPs) is stored on the servers, it’s immediately wiped on each reboot.
The only way WireGuard would put your privacy at risk is if you were to use a shady VPN that uses WireGuard and doesn’t take any measures to prevent IP logging.
Also, keep in mind that, even with top VPNs, some minor form of IP logging still happens. This is simply needed for a VPN connection to be established — otherwise, it won’t work. Don’t worry, though, as this isn’t a concern because top vendors take measures to ensure users’ IPs are encrypted, deleted, and not stored for more than a few seconds or minutes on their servers.
Winner (Privacy): It’s a tie
Both VPN protocols are great for privacy, as they’re both open-source. True, OpenVPN doesn’t require any logging, whereas WireGuard’s default build requires user IP logging on servers — but all the top VPNs that use WireGuard have found ways around that issue to protect their users’ privacy.
WireGuard vs. OpenVPN: Auditability
Both VPN protocols are open-source — this means they provide great transparency, as anyone can inspect the code for security vulnerabilities (even you, if you’re tech-savvy enough). Plus, both WireGuard and OpenVPN have undergone numerous security audits over the years, and the results always stated that both protocols are great for security and privacy.
That said, I think WireGuard has the upper hand — that’s because its library only consists of around 4,000 lines of code. So, it takes less time for auditors to go over the code, and it also makes it much easier to spot potential security or privacy issues and bugs that need to be fixed.
OpenVPN’s library, on the other hand, consists of about 70,000 lines — but that number can go much higher depending on how the protocol is implemented (how many encryption methods are used, for example). So not only does it take much longer to audit the protocol’s code, but the odds of overlooking security and privacy issues also increase.
Winner (Auditability): WireGuard
WireGuard is simply much easier to audit, as its library is around 17 times smaller than OpenVPN’s library — so it takes less time to audit the protocol’s code, and auditors are less likely to miss security holes. That said, OpenVPN still provides excellent privacy and security, and has also passed multiple independent audits.
WireGuard vs. OpenVPN: Bypassing Censorship
In terms of circumventing censorship, OpenVPN is the clear winner since it’s much more likely to work in restrictive countries like China and Russia than WireGuard.
The main reason OpenVPN is better than WireGuard for this is because it can use TCP port 443 (a port is a number used by network protocols for online communication). This is the port that’s used by HTTPS traffic. So, restrictive governments can’t block that port to try and block your VPN connection — if they were to do that, they’d block HTTPS traffic across the country.
WireGuard, on the other hand, can’t use TCP ports, only UDP ports. And UDP port 443 is mostly used by online games, so a restrictive country wouldn’t have any issues blocking it. True, WireGuard can essentially use almost any UDP port, so it might be able to evade port blocking — that said, keep in mind that governments can block port ranges (multiple ports at the same time), so they could easily block WireGuard regardless of how many UDP ports it uses.
Also, OpenVPN supports obfuscation, which is a security feature that hides VPN traffic. This is useful for avoiding Deep Packet Inspection (DPI) blocks in restrictive countries — DPI is a network traffic analysis method that’s used to detect and block VPN traffic. WireGuard, however, doesn’t officially support obfuscation.
Most top VPNs that provide obfuscation only support via the OpenVPN protocol (or via their proprietary protocols). Some exceptions work in restrictive countries via WireGuard, like Astrill VPN, for example — but this is likely because the VPN refreshes its server IPs very fast to avoid IP blocks, not because it uses WireGuard.
Winner (Bypassing Censorship): OpenVPN
If you live in or travel through a restrictive country, you should always use OpenVPN. Unlike WireGuard, it can use TCP port 443 and it also supports obfuscation — both of those things help the protocol avoid censorship. WireGuard might work in restrictive regions, but that’s only if the government uses IP blocks and if the VPN refreshes its server IPs really fast.
WireGuard vs. OpenVPN: VPN & Device Compatibility
Both protocols are compatible with a wide range of mobile and desktop platforms. In addition, it’s also possible to manually set up each protocol on different router models — in case you want to secure all the web-connected devices in your home with just one VPN connection.
Most top VPNs also provide built-in access to OpenVPN and WireGuard on the majority of their apps. For example, Private Internet Access (PIA), CyberGhost VPN, and Surfshark all support WireGuard on their Android, iOS, Windows, macOS, and Linux apps, while Proton VPN has the protocol on all apps except Linux. Also, PIA and Surfshark support OpenVPN on all iOS, Android, Windows, macOS, and Linux. CyberGhost VPN has OpenVPN on Android, Windows, and Linux, while Proton VPN supports it on all apps except iOS.
Winner (VPN & Device Compatibility): It’s a tie
Both WireGuard and OpenVPN provide great compatibility, as they work on tons of devices. What’s more, most top VPNs provide built-in support for these protocols on the majority of their apps — while a few VPNs choose not to include OpenVPN on iOS and macOS apps, this isn’t due to OpenVPN not being compatible with those platforms.
Editors' Note: Intego, Private Internet Access, CyberGhost and ExpressVPN are owned by Kape Technologies, our parent company
WireGuard vs. OpenVPN: Mobility & Data Usage
WireGuard is better for mobility than OpenVPN since it’s designed to resist network changes. Basically, this means your VPN connection won’t drop when you switch networks — like when you switch from a coffee shop’s Wi-Fi to mobile data. OpenVPN doesn’t handle network changes that well, so your VPN might disconnect, which is inconvenient.
Also, because WireGuard is much lighter than OpenVPN, it also uses less mobile data — this might be important if you are on a tight budget or have a very limited data plan. On top of that, WireGuard might also use less of your phone’s battery compared to OpenVPN.
I tested this on my Android smartphone by using Private Internet Access’s app, since it provides access to both protocols. I went out with my friends, and I used the web as I normally would on a night out — but for 2 hours, I used it while connected to PIA (1 hour via OpenVPN UDP, and 1 hour via WireGuard). WireGuard only drained about 4% of my phone battery, and only increased my data usage by about 5%. OpenVPN, on the other hand, drained about 12% of my device’s battery and increased my data usage by around 18%.
Winner (Mobility & Data Usage): WireGuard
WireGuard is simply better in this case. For one, it handles network changes very well (your VPN doesn’t disconnect when you switch from Wi-Fi to mobile data, for example). Also, it uses less of your device’s battery and mobile data than OpenVPN due to its lightweight build.
Overall Winner: WireGuard
While both protocols are really good for security and privacy, and they’re also available on most popular platforms, WireGuard is simply better than OpenVPN. That’s because it’s more lightweight, so it provides significantly faster speeds. In addition, it’s also much easier to audit the protocol’s code. And WireGuard is also good for mobile users, as it resists network changes and uses up less battery and mobile data than OpenVPN.
That said, OpenVPN is great if you’re dealing with VPN blocks, either in restrictive countries or on restrictive networks (at school, for example). Unlike WireGuard, it supports obfuscation and it’s also able to use TCP port 443, so it has an easier time getting around censorship.
Frequently Asked Questions
Is WireGuard faster than OpenVPN?
Yes, WireGuard has significantly faster connection speeds than OpenVPN — I have confirmed this in multiple speed tests. I tested both nearby and distant servers from several VPNs that have both WireGuard and OpenVPN, and WireGuard always maintained much faster browsing, streaming, torrenting, and gaming speeds. This is mostly because WireGuard’s library is much more lightweight than OpenVPN’s library.
Is WireGuard more secure than OpenVPN?
No, I personally think that both protocols provide excellent security. While OpenVPN can use more encryption methods, WireGuard still comes with state-of-the-art encryption ciphers that are extremely strong. True, WireGuard’s default build comes with some privacy concerns, but all the top VPNs that have integrated this protocol into their apps have found a way to fix those issues.
Does WireGuard work in China?
Most likely not, as the protocol is not designed to support obfuscation (a feature that hides VPN traffic) or use TCP port 443, which is the same port that’s used by HTTPS traffic. So, a restrictive government would be able to block WireGuard connections via VPN traffic blocks and port blocking. I generally recommend that people who live in or are traveling through restrictive countries use OpenVPN instead.
Which is better for privacy — WireGuard or OpenVPN?
Both protocols are really good for protecting your privacy, to be honest. True, WireGuard’s default build has some privacy issues that require the logging of VPN users’ IP addresses. That said, most top vendors that use WireGuard have found ways around that issue, from using RAM-only servers to modifying the server’s data output.