Hacker and Activist Noam Rotem, working with Safety Detectives research lab, was shocked when he recently discovered a major vulnerability affecting nearly half of all airlines worldwide. While booking a flight with Israeli national carrier ELAL, he came across a significant security breach that allows anyone to access and change private information on flight bookings. The same breach was then discovered to include 44% of the international carriers market, potentially affecting tens of millions of travelers.
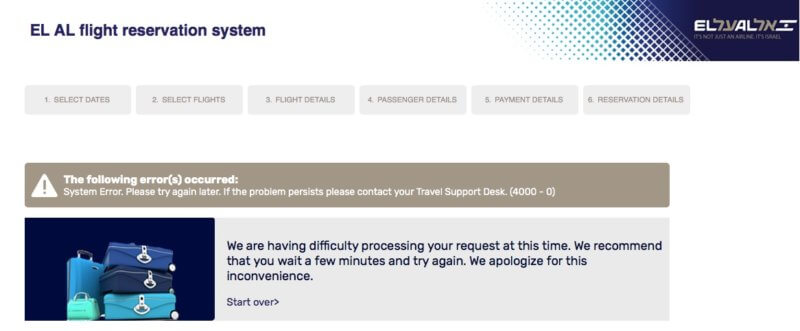
According to ELAL, the bug stems from their supplier Amadeus’ (https://amadeus.com/en/industries/airlines) online booking system, which controls a staggering 44% market share of airlines operating worldwide, including United Airlines, Lufthansa, Air Canada, and many more. While booking a flight with ELAL, we received the following link to check our PNR: https://fly.elal.co.il/LOTS-OF-NUMBERS-HERE.
By simply changing the RULE_SOURCE_1_ID, we were able to view any PNR and access the customer name and associated flight details.
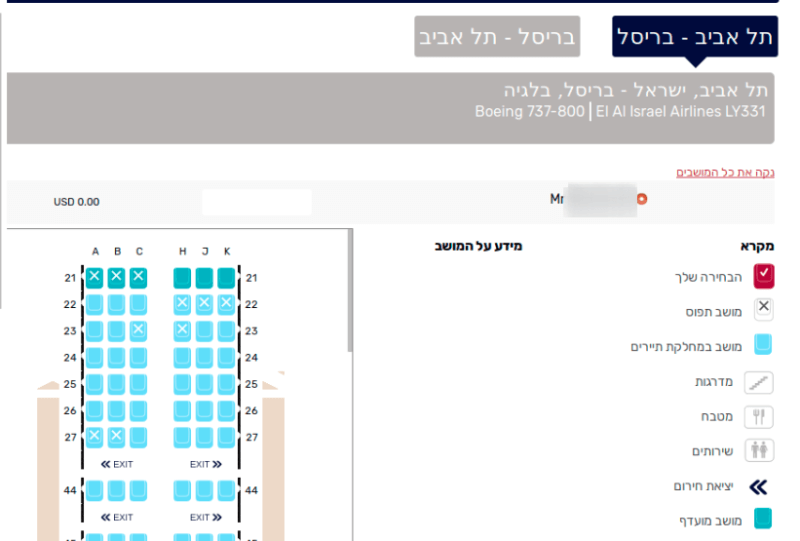
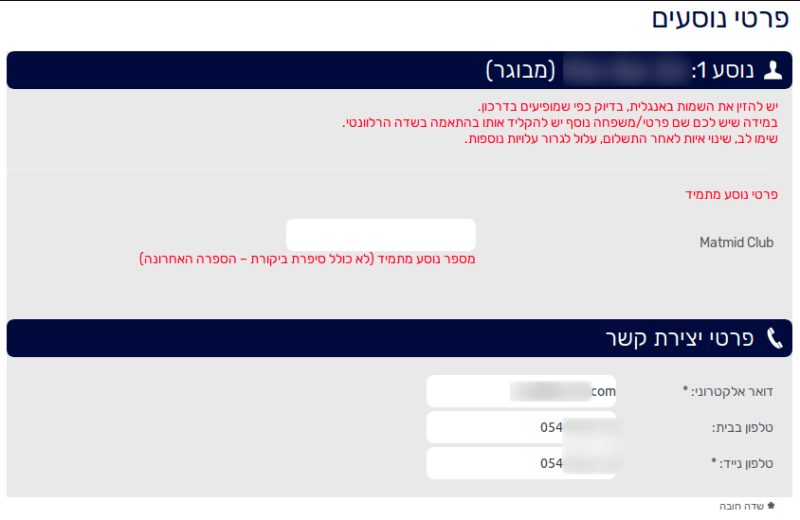
With the PNR and customer name at our disposal, we were able to log into ELAL’s customer portal (https://booking.elal.co.il/newBooking/changeOrderNewSite.jsp) and make changes, claim frequent flyer miles to a personal account, assign seats and meals, and update the customer’s email and phone number, which could then be used to cancel/change flight reservation via customer service.
Though the security breach requires knowledge of the PNR code, ELAL sends these codes via unencrypted email, and many people even share them on Facebook or Instagram. But that’s just the tip of the iceberg.
After running a small and non-threatening script to check for any brute-force protections, none of which were found, we were able to find PNRs of random customers, which included all of their personal information. We contacted ELAL immediately to point out the threat and prompt them to close the breach before it was discovered by anyone with malicious intentions.
We suggested stemming the vulnerability by introducing captchas, passwords (in place of a 6-character PNR code), and a bot protection mechanism, in order to avoid using a brute-force approach.
The below screenshots show the options we could change for every flight (in Hebrew). The same vulnerability existed for all 141 airlines using the Amadeus system until it was fixed earlier this week.
Replacing seats
Changing contact details and applying frequent flyer.
A simple script we devised guessed the PNR numbers and was able to find active numbers in Amadeus. Now that the issue has been fixed, the script can no longer identify active PNRs as demonstrated in this video:
When contacted about the breach, Amadeus provided the following statement:
“At Amadeus, we give security the highest priority and are constantly monitoring and updating our systems. Our technical teams took immediate action and we can now confirm that the issue is solved. To further strengthen security, we have added a Recovery PTR to prevent a malicious user from accessing travelers’ personal information. We regret any inconvenience this situation might have caused.”
You may also want to read about why we consider Kaspersky a virus and how to hack ethically.
Published on: Jan 15, 2019