The SafetyDetectives cybersecurity team has discovered a leaked SQL database appearing to belong to the RedAwning vacation platform.
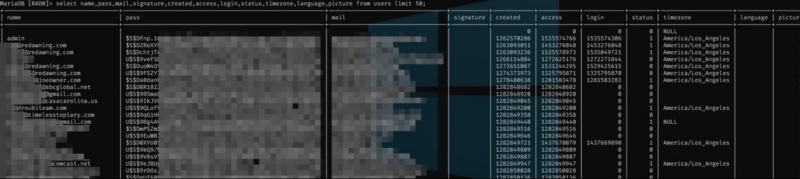
A user on the forum posted the database for free, which is now available for the public to view. According to our researchers, the database is exceptionally well-organized and easy to search. So, our researchers were able to ascertain that the alleged data breach likely impacts approximately 45,000 registered users.
Who is RedAwning?
RedAwning.com is an online travel agency that enables tourists to find and book vacation properties worldwide. Founded in 2010, the California-based organization provides marketing, distribution, reservation, and hospitality solutions to customers in the United States.
The company uses the slogan, “Travel boldly, we’ve got you covered” and claims to be “the largest branded collection of vacation properties in the world offering hotel-like reservation and support services.”
According to the organization, its partners include Airbnb, Booking.com, Expedia, Trivago, and Agoda. RedAwning recently acquired Lexicon Travel Technologies, a US channel manager.
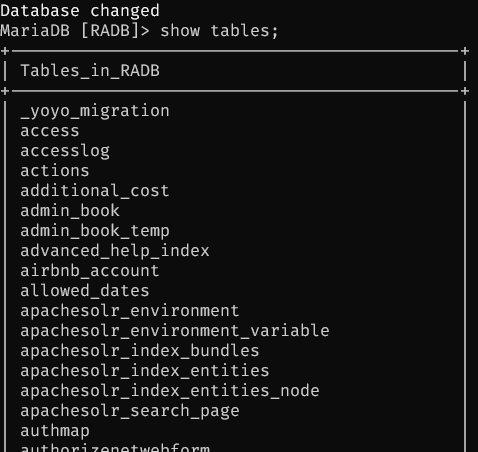
What is the forum about?
The website where the database was found is a forum available on the clear, surface web. The community forum includes tutorials for crack tools, exploits, and software.
Forum members are able to post and promote database leaks. There is also a marketplace for purchasing digital products and services, including cracked accounts, fraudulent tokens, and credit card dumps.
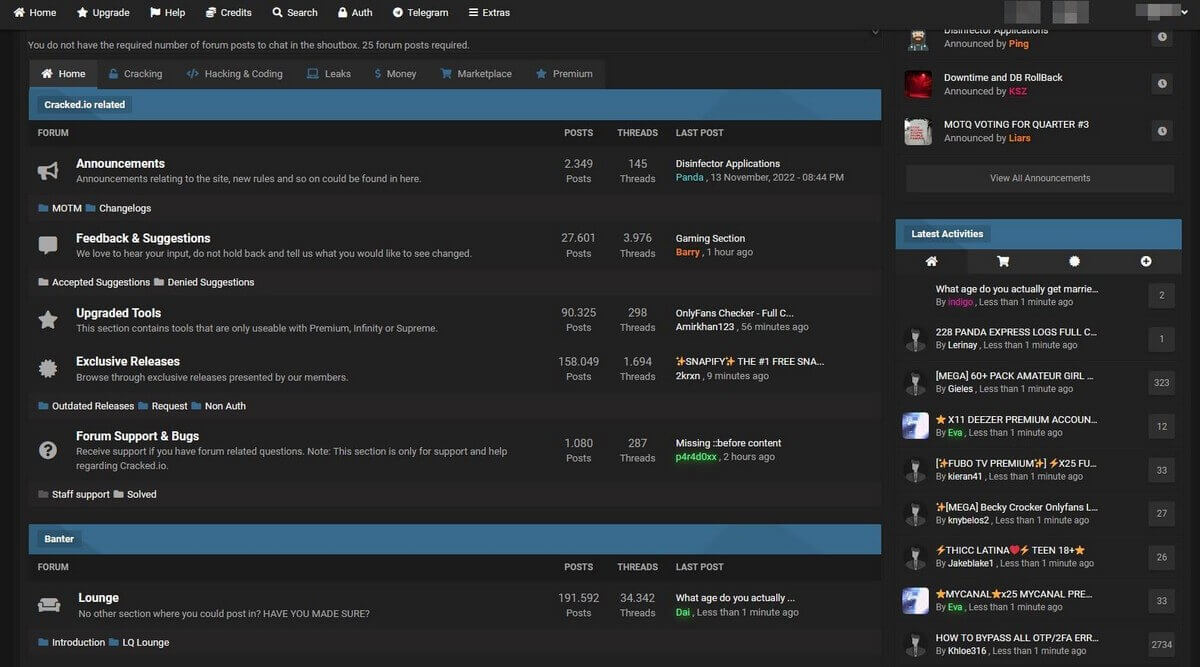
Screenshot of the forum’s landing page
Exposed information:
The likely date of the breach was on or around September 6, 2018. We base this assumption on our analysis of recorded timestamps contained in the database. In order to determine an exact date of breach, we would have to comb through the entire exposed SQL database but we chose not to for ethical reasons.
The forum post is dated November 10, 2022, and was published by a forum member. SafetyDetectives discovered the forum post containing details about the data breach on November 16.
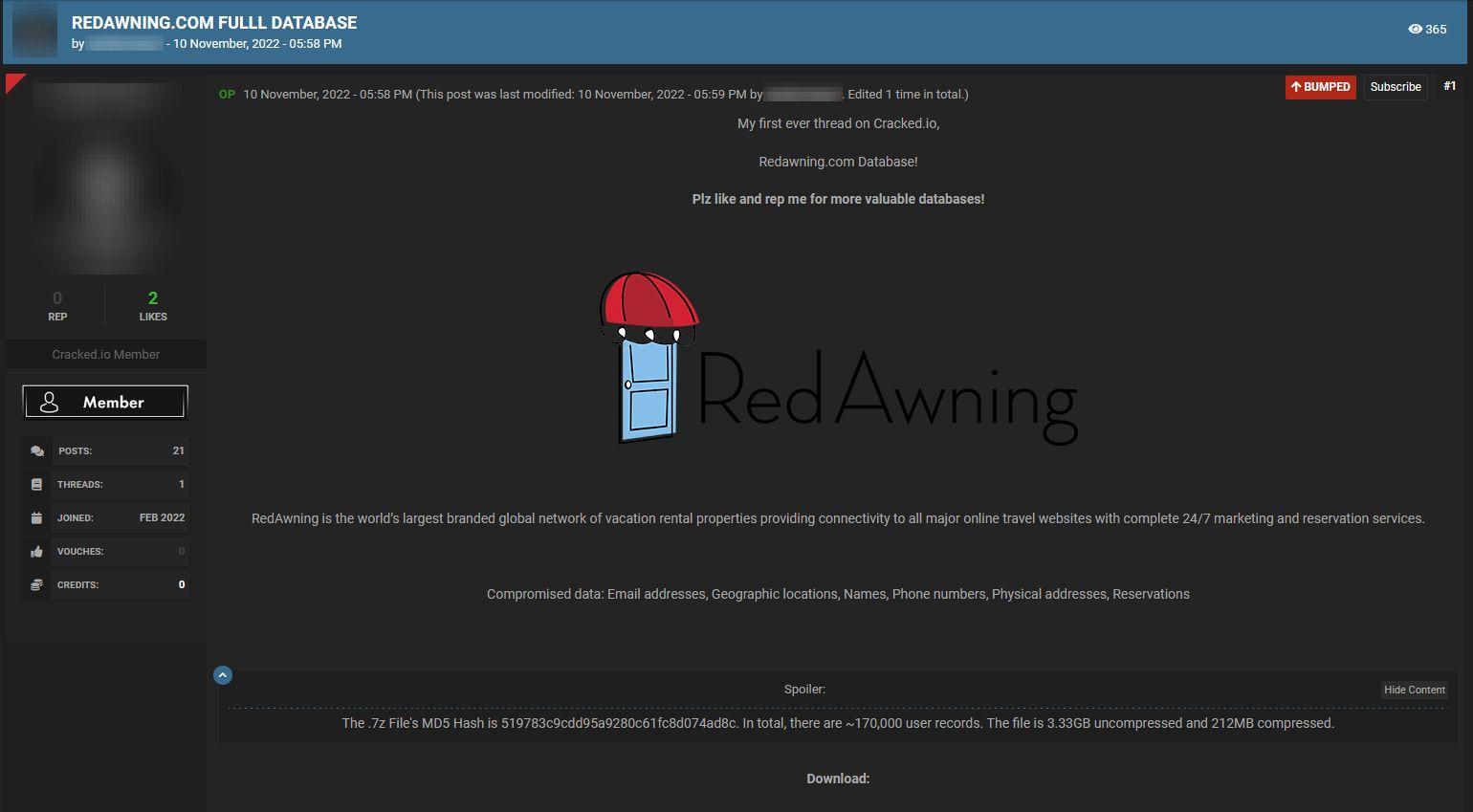
Screenshot of the forum post
The forum post reads:
“RedAwning is the world’s largest branded global network of vacation rental properties providing connectivity to all major online travel websites with complete 24/7 marketing and reservation services.
Compromised data: Email addresses, Geographic locations, Names, Phone numbers, Physical addresses, Reservations
The .7z File’s MD5 Hash is 519783c9cdd95a9280c61fc8d074ad8c. In total, there are ~170,000 user records. The file is 3.33GB uncompressed and 212MB compressed.”
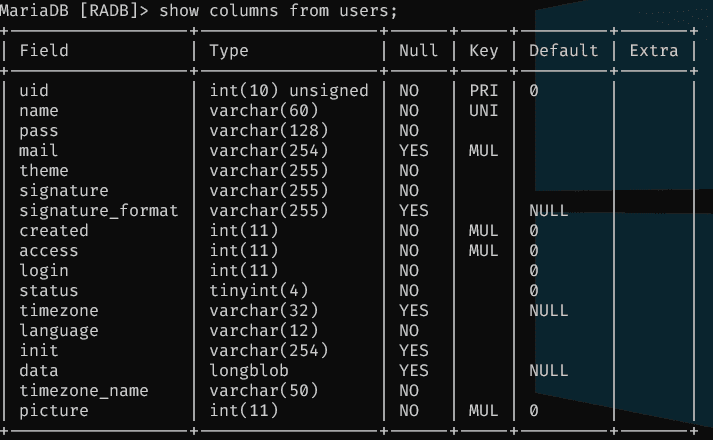
The database was said to contain 3.3GB of uncompressed data, containing 28,658,749 records, including Personally Identifiable Information (PII) such as names, phone numbers, and physical addresses. Based on further analysis, our researchers estimate that in total, there appears to be at least 87,000 further, unregistered users included in the records.
SafetyDetectives researchers estimate that 45,000 registered users are included in the leak of the 3.3GB SQL database.
Considering the size of RedAwning, said to have served close to one million customers to date, it is unclear if the leak only included a small portion of RedAwning’s overall database, or if the users referred to are property owners rather than holidaymakers.
The impact of the data breach:
At this time, it is not possible to say how long the SQL database was exposed or if the database continues to be open and accessible today.
The data dump appears to include the Personally Identifiable Information (PII) of RedAwning users, including their first names, last names, cities of residence, email addresses, hashed passwords, booking dates, and cell phone numbers.
The exposed data would have been enough for skilled cybercriminals to commit many of the most common forms of fraud or online attacks against allegedly compromised RedAwning users, including:
- Identity theft
- Phishing campaigns
- Doxing and harassment
Timeline:
- September 6, 2018: The likely date of the alleged data breach
- November 10, 2022: The link to the SQL database was posted online
- November 16, 2022: The data dump was found by SafetyDetectives
We have reached out to the database owners, and they replied on December 20th, 2022, telling us that they’re aware that an old copy of some data was on the dark web and asked us to share details about our findings. Please find below their reply:
“* The leak was not the result of a security “breach” or hack of our infrastructure. There is no ongoing security issue.
* The leak occurred when a copy of a database was downloaded for local development purposes to a developer’s laptop and that laptop was subsequently lost.
* The SQL database in question is a copy of a “stage” (test/development) database created in 2018.
* The Stage database contains mostly test (fake) data.
* Some actual customer data (fewer than 10,000 records) was replicated into the Stage database, likely prior to 2016, for additional testing purposes.
* The customer data includes names and email addresses, and in some cases mailing addresses and phone numbers along with booking dates.
Since 2018 (when the leak occurred) we have implemented additional security measures, including full database encryption at rest and the removal of any SQL file copies of our databases.
RedAwning takes security seriously and we sincerely appreciate your sharing what you have found.”
Preventing data exposure:
When third parties hold your data, unfortunately, it is out of your hands when an organization exposes information. Here are some preventative tips and guidance on what happens after you are made aware of a data breach.
- Be cautious of what information you give out and to whom
- Check that the website you’re on is secure by looking for HTTPS in the address bar, and/or a closed lock). This shows that communication has at least a basic level of encryption. It would help if you also used a VPN to disguise and secure your online activity.
- Only reveal online what you feel confident cannot be used against you. Avoid sharing or posting sensitive PII, images, or personal preferences that could be troublesome if made public.
- Create secure passwords by combining letters, numbers, and symbols, and consider using a password locker to store complex combinations securely.
- Do not click links or respond to emails unless you know the sender is legitimate. Fraudulent links can send you to malicious websites or expose you to exploit kits, whereas phishing emails are designed to steal your information.
- Double-check any social media accounts (even ones you no longer use) to ensure that the privacy of your posts and personal details are visible only to people you trust.
- Avoid using credit card information and typing out passwords over unsecured WiFi networks.
You can use tools including HaveIBeenPwned, as well as read our research and keep an eye on the news to find out if you are potentially involved in a data security incident.
If you suspect your data has been leaked, don’t panic. Nevertheless, it would be best if you tried contacting the organization responsible to discover exactly what happened. Furthermore, you should keep an eye on your credit report and your financial accounts for any signs of suspicious activity indicative of identity theft or fraud.
About us:
SafetyDetectives tests, compares, and reviews antivirus software, password managers, parental control apps, and virtual private networks (VPNs) using a robust testing methodology.
The SafetyDetectives research lab is a pro bono service that aims to help the online community defend itself against cyber threats. We aim to help the online community defend itself against modern-day cyberattackers while educating organizations on how to protect their users’ data.
Find out more about what constitutes cybercrime, the best tips to prevent phishing attacks, and how to avoid ransomware by following SafetyDetectives’ blog and our latest news.