One of India’s most popular travel booking hubs was left exposed without adequate security measures, and subsequently, suffered a significant data breach that exposed all production server information and led to the loss of over 43GB of data.
The affected Elastic search server was left publicly exposed without password protection or encryption for several days which meant anyone with the server’s IP address, could have gained access to the entire database.
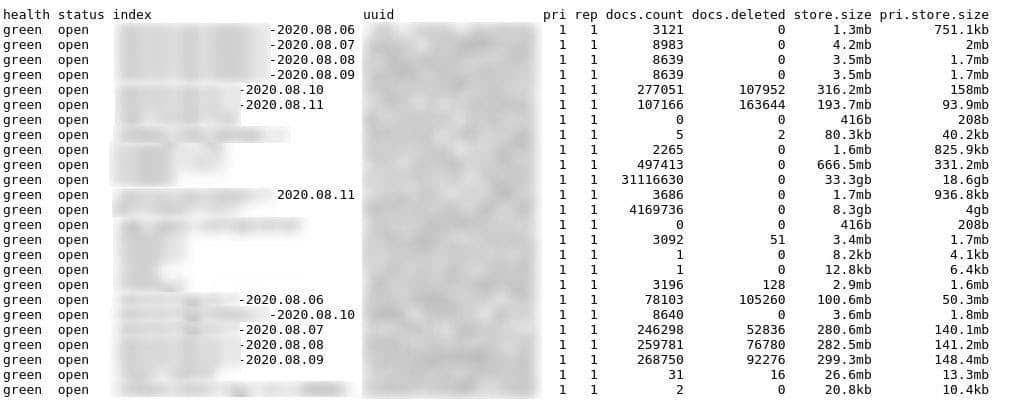
Our security team, led by Anurag Sen, discovered the server vulnerability on 10 August 2020 after it became exposed on the Internet on 9 August 2020. Three days later on 12 August 2020, our team reviewed the data, the server became the target of a Meow bot attack, leading to the deletion of almost all server data.
Most of the affected users were based in India with our team estimating that around 700,000 individuals were likely to be directly affected by the breach.
As a means of resolving the security breaches our team discovered, Safety Detectives informed the affected company as soon as practically possible. Failing to receive a reply regarding the data breach, our team reported its findings to the Indian national Computer Emergency Response Team (CERT-In), a government agency responsible for national cybersecurity. The server was secured the following day.
Who is RailYatri?
Founded in 2011, RailYatri is a government-sanctioned Indian travel marketplace that currently serves a travel network with around 24 million passengers per day. The company sells bus and train tickets for domestic Indian travellers and operates via the web and through an app, available on both the App Store and Google Play.
According to RailYatri’s website, the company develops and operates a complete train app which enables users to book Indian Railway Catering and Tourism Corporation (IRCTC) bus and train tickets, check live train times, journey progress, offline timetables, check seat availability and offline GPS train status.
Also, the travel hub has previously won the Billionth South Asia Award and the Best Utility Award in the Vodafone Appstar contest.
As of the start of August, RailYatri’s mobile app has been downloaded more than 10 million times via Google Play.
What was leaked?
Shown below, is a list of the type of information discovered on RailYatri’s unsecured server:
- Full names
- Age
- Gender
- Physical addresses
- Email addresses
- Mobile phone numbers
- Payment logs
- Partial records of credit and debit card information
- Unified Payment Interface (UPI) ID
- Train and bus ticket booking details
- Travel itinerary information including which stations passengers boarded/disembarked
- Users’ GPS location information including MCC, MNC, LAC and CellID data:
- MCC: mobile country code to identify country
- MNC: mobile network code to identify mobile operator
- LAC: location area code to identify pockets of base stations
- CellID: unique number to identify each base transceiver station or sector
- Authentication token information
- User session logs including login times
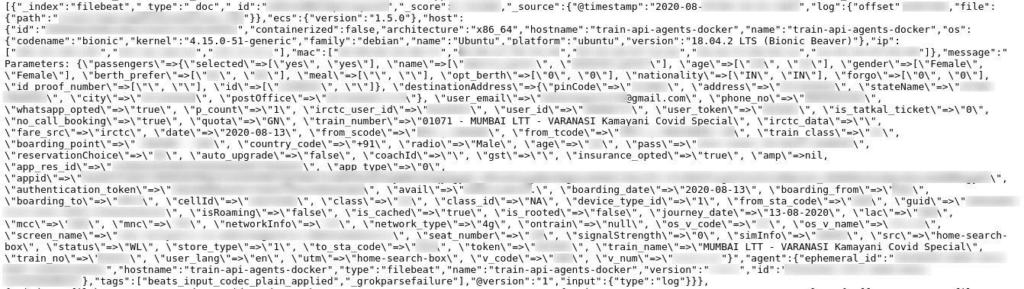
Possibly the most damaging aspect of the data breach is the fact that our security team discovered partial credit and debit card payment logs including the name on the card, the first and last 4 digits of the card number, the card-issuing bank and card expiry information.
Thankfully, the leaked payment information was suppressed to reveal only partial copies of card numbers. This drastically reduces the chance of a malicious financial scam; however, resourceful hackers could still use the information on the server to launch phishing scams to induce victims to hand over their financial information.

Furthermore, our team found that authentication token data was attached to the majority of URLs.
On 12 August 2020, RailYatri’s database was attacked by a malicious bot called Meow with the vast majority of data being deleted during the intrusion.
At the most recent check done on 13 August 2020, the database’s size had shrunk from 43GB to 1GB, although new data is being added on a daily basis.
Server logs did not indicate the precise number of users affected by the intrusion. However, according to our security team, the database contained over 700,000 email addresses, which, despite some being duplicated, indicates that approximately 700,000 people were affected by the breach.
Data Breach Impact
The obvious dangers of personally identifiable information (PII) being made public are extensive. Any small piece of seemingly innocuous information can be collated by malicious actors, to be used later or in parallel with other information in order to deceive the intended target.
Exposed user information could potentially be used to conduct identity fraud across different platforms and other sites. Users’ contact details could be harnessed to conduct a wide variety of scams while personal information from the breach could be used to encourage click-throughs and malware downloads. Personal information is also used by hackers to build up rapport and trust, with a view of carrying out a larger magnitude intrusion in the future.
On this particular occasion, our team’s discovery and consequent contact with RailYatri to assist in securing their server proved to be insufficient in preventing a major server intrusion that led to more than 90% of the server’s database being lost.
Another key risk from the leaked data is location data. RailYatri’s server recorded and stored users’ location information when booking their tickets, and also allowed users to track their journey progress with integrated GPS functionality. This information could be used by hackers to locate the nearest cell tower to the user, and potentially, the user’s actual location including current address.
Moreover, and from an offline perspective, regular train users generate clear and distinguishable travel patterns which malicious actors could use to commit violent crime directly upon the individual.
Preventing Data Exposure
How can you prevent your personal information from being exposed in a data leak and ensure that you are not a victim of attacks – online or offline – if it is leaked?
- Be cautious of what information you give out and to whom
- Check that the website you are visiting is secure (look for the https and/or a closed lock symbol in the address bar)
- Only give out what you feel confident cannot be used against you (avoid government ID numbers, personal preferences that may cause you trouble if made public)
- Create secure passwords by combining letters, numbers, and symbols
- Do not click emailed links unless you are sure that the sender is legitimate
- Double-check any social media accounts (even ones you no longer use) to ensure that the privacy of your posts and personal details are visible only to people you trust
- Avoid using credit card information and typing out passwords over unsecured Wi-Fi networks
- Check out our Known Vulnerabilities Scanner tool
- Find out more about what constitutes cybercrime, the best tips to prevent phishing attacks, and how to avoid ransomware
About Us
is the world’s largest antivirus review website.
The Safety Detective research lab, headed up by Anurag Sen, is a pro bono service that aims to help the online community defend itself against cyber threats while educating organizations on how to protect their users’ data.