Updated on: September 15, 2024
Vietnamese medical company suffers devastating data leak
Led by Anurag Sen, the Safety Detectives cybersecurity team discovered an unsecured ElasticSearch server belonging to the Vietnamese company Innovative Solution for Healthcare, better known as iSofH.
The technology company provides medical information management solutions in Vietnam, and caters for both private and public sector clients. In early November 2020, our team discovered that the company suffered a devastating data leak affecting more than 80,000 people affecting both customers, and potentially, company staff, given the extensive range of personal information that was made available publicly without adequate security measures.
Moreover, it appeared that the tech company bore the brunt of a concurrent Meow bot cyberattack that removed an unknown amount of records.
The company’s server vulnerability was discovered during a routine IP address check via a particular range of ports. Our team discovered the Elasticsearch server to be publicly exposed without encryption or password protection.
Who is Innovative Solution For Healthcare (iSofH)?
iSofH is a leading Vietnamese technology company providing medical information management solutions in the Vietnamese market. The company’s software solutions are deployed at 18 medical facilities in Vietnam including 8 top-tier National Hospitals and Clinics.
iSofH’s software is also used at Hospitals under the Department of Health; Hospitals under the Ministry of Public Security, the Ministry of Defense and a number of general clinics in Hanoi.
The company’s products include hospital management software, electronic medical records safekeeping, mobile phone apps and online counselling services. Given the detailed nature of people’s varied medical needs, iSofH was responsible for safeguarding extremely sensitive information relating to people’s personal lives and medical records.
What was leaked?
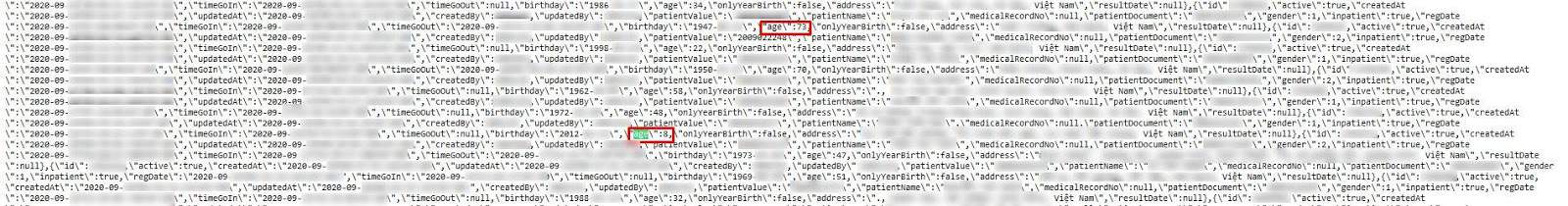
iSofH’s server contained API logs for both its web and mobile sites, exposing URL queries made by its users. Leaked data revealed internal system details including file paths and directory locations which could be exploited by hackers.
Our security team discovered records from multiple services and platforms provided by iSofH to various hospitals under the purview of Vietnam’s Ministry of Health.
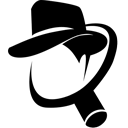
According to their website, iSofH is providing services to https://quanlytrangthietbiyte.com – a public portal owned by the Vietnamese Ministry of Health used for publishing prices of medical equipment.
A further operational connection between iSofH and quanlytrangthietbiyte.com was discovered in the form of an SSL certificate that named quanlytrangthietbiyte.com as the issuer for iSofH’s Elasticsearch server.

Server information showing SSL certificate registered on “https://quanlytrangthietbiyte.com”
The leak also exposed data related to companies who registered on https://quanlytrangthietbiyte.com such as tax number, email address, company name and address, etc.
The database contained more than 12 million records totalling more than 4GB of data with at least 80,000 people affected by this breach.
The following personally identifiable information, exposing patients, company employees and medical staff was publicly available on iSofH’s Elasticsearch server:
- Full name
- Date of Birth
- Gender
- Postal address
- Phone number
- Email Address
- Patient medical records
- Recent test results and diagnoses
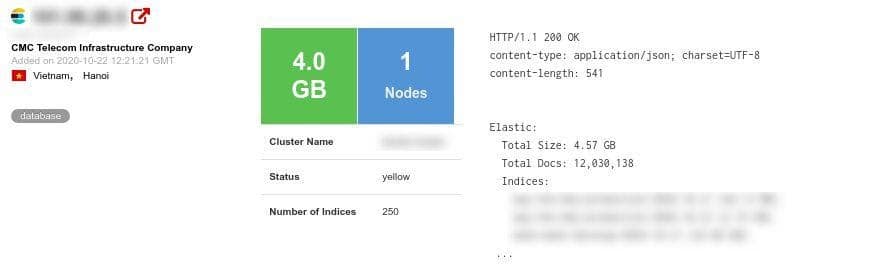
- Passport details including passport number, issue date and place
- Credit card number
Furthermore, our team discovered encrypted strings for “frontPassport” and “backPassport”, which potentially store passport pictures. In accordance with ethics and privacy guidelines, our security team did not attempt to decrypt the files.
Our team discovered evidence that iSofH’s server potentially contained personal employee data, although this cannot be conclusively corroborated.

Possibly most alarming of all, the affected server contained patient diagnoses which were stored without password protection or encryption.
It is worth noting that a large portion of the leaked data was in Vietnamese which significantly slowed our analysis of the data. To confirm our findings and make sure our understanding was correct, we referred to a native Vietnamese speaker working with us who helped us with the translation of anonymized screenshots.
Their translation confirmed our findings that iSofH kept incredibly detailed records for all patients including diagnoses, dates, specific “disease codes” on both admission and discharge, doctor ID numbers and insurance coverage details.
Other bits of information were also included in the leak such as:
- Medical equipment sale information
- Multiple hospital bidding and registration information
- API logs including access tokens
Notably, the server vulnerability revealed personal information belonging to minors including their full name, date of birth, gender and address.
With regards to both adult and minors information, not every user record contained all the details meaning that although some user records were fully complete, the vast majority were not.
iSofH’s cybersecurity vulnerability was identified by our security team in late October although it remains unknown as to when the vulnerability was first created. The information stored in the database was in Vietnamese which impeded our ability to determine what data was leaked and who should have rightful access to it.
Unfortunately, three days after the database vulnerability was discovered, it was attacked by the Meow bot which deleted some of its indexes.
The “Meow bot” is a sophisticated form of cyberattack that uses automated software to seek and destroy the content of unsecured Elasticsearch databases. The bot’s name is derived from the fact that it overwrites the word “meow” repeatedly in each database index that it detects.
Our security team reached out to iSofH and the Vietnamese CERT mid-November 2020, but has not received a response from either party. Our team also contacted the hosting company responsible for the server, with the same result.
Finally, we attempted to contact https://quanlytrangthietbiyte.com regarding the server vulnerability, given the fact that their data was also affected. Despite our numerous attempts to contact all parties involved, we have not received a response to any of our notifications.
At the end of December 2020, our team reached out to the Vietnamese CERT for the second time. They finally got back to us which allowed us to proceed to a responsible disclosure. They acknowledged the existence of the open server but failed to see the sensitivity of it. We tried to explain our findings, hoping they’ll realize how critical the leak was.
Data Breach Impact
The impact of this data breach is devastating, both for the end-users whose personal information was leaked, but also for the broader medical industry in Vietnam because of the company’s connections to national infrastructure and the country’s health ministry. The leak compromises the privacy of thousands of people and could have potentially pushed Vietnam’s entire national health infrastructure into disrepute.
Incredibly sensitive medical conditions such as diagnoses for life-changing conditions and medical test results attached to PIIs were exposed which could potentially lead to blackmail, extortion, and other scams.
Importantly, the server contained incredibly detailed patient information and logs, as well as, personal information regarding company staff and even partial information about the doctors who work at the various hospitals iSofH operates. If such information was to fall into the hands of criminals, this would present an acute security risk to doctors, company staff and patients simultaneously.
More broadly, revealing full names, addresses and emails can be harnessed by nefarious users to inflict severe financial and reputational harm upon victims in the form of identity theft and financial fraud. The availability of credit card information further exacerbates the potential danger posed to victims, leaving them susceptible to credit card fraud and other financial crimes.
Preventing Data Exposure
How can you prevent your personal information from being exposed in a data leak and ensure that you are not a victim of attacks – cyber or real-world – if it is leaked?
- Be cautious of what information you give out and to whom
- Check that the website you are on is secure (look for https and/or a closed lock)
- Only give out what you feel confident cannot be used against you (avoid government ID numbers, personal preferences that may cause you trouble if made public, etc.)
- Create secure passwords by combining letters, numbers, and symbols
- Do not click links in emails unless you are sure that the sender is legitimately who they represent themselves to be
- Double-check any social media accounts (even ones you no longer use) to ensure that the privacy of your posts and personal details are visible only to people you trust
- Avoid using credit card information and typing out passwords over unsecured Wi-Fi networks
- Find out more about what constitutes cybercrime, the best tips to prevent phishing attacks, and how to avoid ransomware
About Us
is the world’s largest antivirus review website.
The Safety Detective research lab is a pro bono service that aims to help the online community defend itself against cyber threats while educating organizations on how to protect their users’ data. The overarching purpose of our web mapping project is to help make the internet a safer place for all users.
Our previous reports have brought multiple high-profile vulnerabilities and data leaks to light including 3 gigabytes of scraped Facebook user data affecting 12 million users, also in Vietnam, as well as, around 2 million users’ information being leaked by Indian e-learning platform Edureka.
For a full review of Safety Detectives cybersecurity reporting over the past 3 years, follow SafetyDetectives Cybersecurity Team.