
Updated on: October 18, 2024
Short on time? Here’s how to remove the COM Surrogate virus:
- 1. Scan Device — Scan your PC using a trusted antivirus (Norton has an excellent virus scanner).
- 2. Remove Virus — If the antivirus detects the COM Surrogate virus, let the antivirus remove all instances of the virus and any malicious files related to it.
- 3. Stay Protected — Keep your PC protected against other viruses, malware, and online threats by using a trusted internet security software (again, Norton offers effective protection against all kinds of threats, including anti-phishing tools, email protection, a secure VPN, and advanced dark web monitoring).
COM Surrogate is a normal Windows process, but hackers use fake versions of it to infect a PC while avoiding detection. The COM Surrogate virus is one of the most common malware infections on Windows computers — it’s pretty dangerous, but getting it off of your PC actually isn’t very hard.
However, you should never try to delete the COM Surrogate virus manually. If you attempt to remove the virus manually, you risk causing permanent damage that can lead to Windows 10 failing completely.
The most efficient and secure way to remove the COM Surrogate virus is by installing a comprehensive antivirus suite. A good antivirus will not only quarantine and remove every instance of the COM Surrogate infection from your computer, but it will also ensure you remain safe from future threats with its real-time protection and scanning capabilities.
I recommend Norton as the best antivirus to remove the COM Surrogate virus. Norton has an advanced malware scanner with flawless detection rates, and you can get it for just $54.99 / year*. Plus there’s a 60-day money-back guarantee, so you can try it for 2 months risk-free.
Try Norton (60 Days Risk-Free)
Preliminary Step: Checking for a COM Surrogate Infection
If you want to check whether the COM Surrogate process running on your system is malware, you must first understand what the standard COM Surrogate process is.
Think of COM Surrogate as a behind-the-scenes helper for your computer. Officially known as Component Object Model (COM), it’s like a middleman that helps your computer’s various parts talk to each other more efficiently. For instance, when you open a folder with pictures and see those mini-preview images (thumbnails), that’s COM Surrogate working to generate them on the fly.
So, why do hackers like to impersonate this helper? Because it’s so integral to your computer’s operation, disguising malware as COM Surrogate can give them a backdoor to your system — allowing them to sneak in unnoticed and gain control.
That said, here’s how to know if you’re looking at an authentic instance of COM Surrogate or a dangerous piece of malware:
Bring up your Task Manager by hitting CTRL + Shift + ESC.
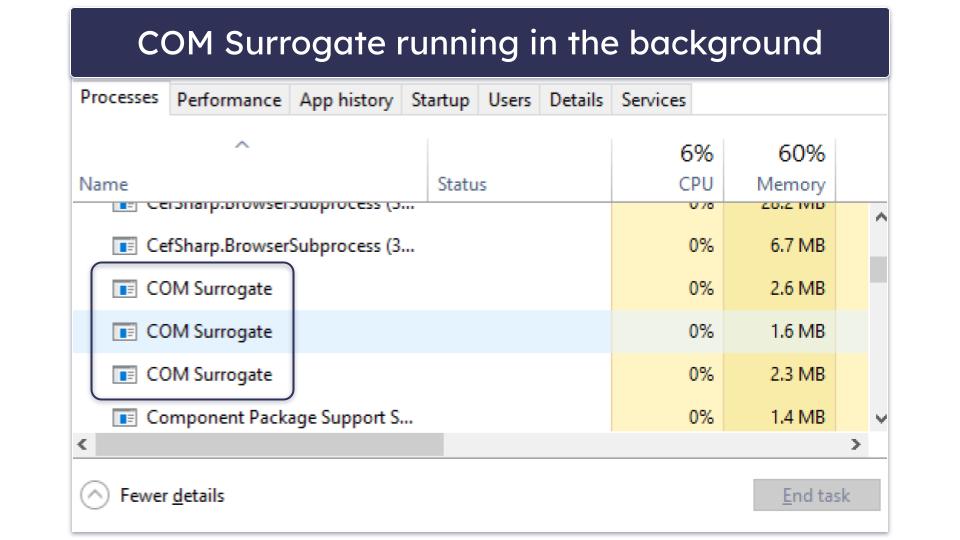
In the picture above, you can see COM Surrogate is running 3 times on the system. While this may look alarming, it’s not. It simply means multiple applications are using the middleware to help them communicate with the OS.
To confirm this, you can right-click on both instances and click Open File Location. If they go to a file called “dllhost.exe” in the System32 folder on the system, then it is unlikely they are malicious.
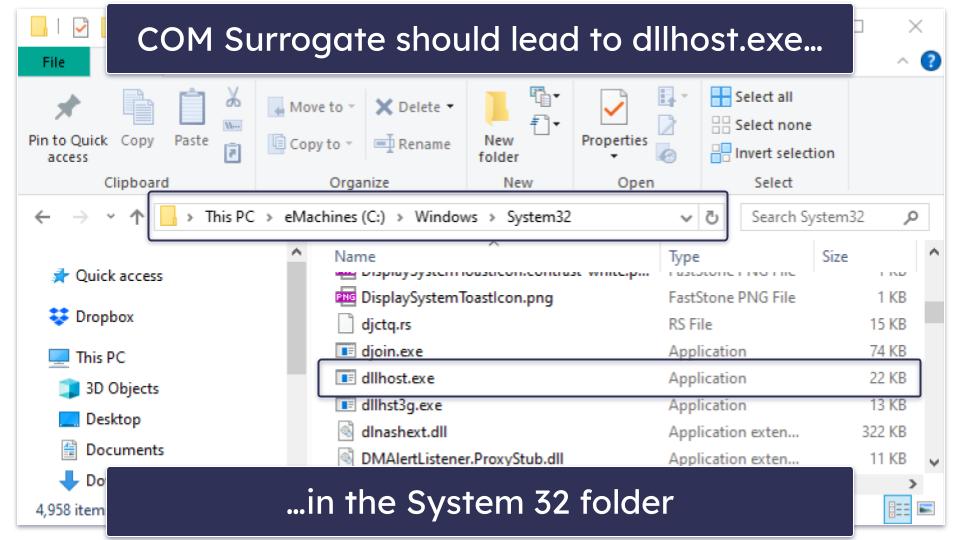
If the file is located anywhere other than dllhost.exe, then you have a virus and should follow my removal steps.
Step 1. Identify the COM Surrogate Virus With Your Antivirus (And Don’t Make the Problem Worse!)
Now that you’ve downloaded a secure antivirus program, you can run a full disk scan to identify the COM Surrogate virus and any other malware on your computer. It’s really important to let the scan run to completion, because even if you think you know where the infection started or the suspicious file is located, it might have replicated itself elsewhere on your system. So don’t be tempted to cancel the scan once you see the virus appear on the infected file list.

The full disk scan will detect and quarantine all instances of the COM Surrogate virus, and make sure your computer isn’t infected with other malware like spyware, worms, or rootkits. It can take between 1 and 4 hours, so be patient as it analyzes every file and process on your computer.
The antivirus will inform you when the scan is complete — now every piece of malware on your computer, including the COM Surrogate virus, has been identified and put into quarantine! It’s time for the next step.
Step 2. Remove the COM Surrogate Virus Infection and Delete Any Other Infected Files
Now that the full disk scan has identified and quarantined any compromised files, you’ll be given the option to delete them. More technical users can go through the files one by one and check for false positives before hitting Delete. But if you’re less techie, it’s fine to just trust the antivirus to do its job — a quality program like Norton is unlikely to generate lots of false positives anyway.

Once you’ve deleted the files, you should restart your computer. Then, run another full disk scan to make absolutely certain that your antivirus has removed every trace of the COM Surrogate infection. Usually, the second scan will be quicker — Norton, and many other antiviruses, are able to remember which files they’ve already scanned and avoid scanning them again next time round.
Once again, it’s important to let the antivirus complete its scan so that you know your whole system has been fully checked. When it’s finished, and you’re not seeing any more infected files, you can be confident that your computer is totally malware-free! For now, that is.
Unfortunately, there is a huge quantity of malware out there that can infect your computer, compromise your accounts, and even spread through your Wi-Fi network. Read on to find out what you can do to avoid getting reinfected.
Step 3. Keep Your Device From Getting Re-Infected
Since the COM Surrogate virus has already infected your computer, you’ve witnessed first-hand how easy it is to get malware on your PC. There are new malware threats released every day, as hackers exploit vulnerabilities in software to gain access to your system. Plus, there’s the danger of identity theft, online data harvesting, and your Wi-Fi getting hacked.
The best thing you can do today is install a reliable antivirus software that is designed to protect your PC from viruses and other cybersecurity threats. Reliable antivirus programs, like Norton and Bitdefender, come with comprehensive security features that detect hidden viruses and prevent you from downloading and installing malware. These antivirus programs had perfect malware detection rates in my tests and stopped trojans, rootkits, computer worms, adware, spyware, and more.
Best Antivirus Programs to Remove COM Surrogate in 2024
Quick summary of the best antiviruses to remove COM Surrogate in 2024:
- 🥇1. Norton — Best antivirus for removing COM Surrogate (perfect detection rates).
- 🥈2. Bitdefender — Lightweight antivirus to remove malware, plus ransomware protection.
- 🥉3. TotalAV — Best cleanup tools after deleting malware + phishing protection.
Tips for Protecting Your Device From the COM Surrogate Virus & Other Malware
Aside from antivirus protection, how else can you keep your devices and data safe in today’s online world? There are several things you can do:
- Regularly back up your personal files — Regularly backing up your personal files will ensure you can reinstall Windows and remove any malware without losing data. Norton 360 Deluxe comes with 50 GB of cloud storage, so you can easily back up important files. If you’re in the US, you can choose a LifeLock plan and get up to 100 GB of cloud storage.
- Turn on User Account Control (UAC) — UAC is a built-in security feature in Windows that prevents applications from making changes to your operating system without your permission. To turn on User Account Control:
1. Open your computer’s Start menu and navigate to the Control Panel.
2. Click System and Security.
3. Click Change User Account Control settings.
4. Drag the slider up to Always notify.
5. Click OK.
6. Click Yes on the pop-up that Windows issues. - Turn on Tamper Protection — Tamper protection is another security feature in Windows that prevents malware from modifying or disabling certain features, including your antivirus. To enable tamper protection:
1. Type in Windows Security in your computer’s search bar and click Windows Security.
2. Click Virus & threat protection.
3. Under Virus & threat protection settings, click Manage settings.
4. Scroll down until you see Tamper Protection and switch it to On. - Enable multi-factor authentication — Many services, including your Microsoft account, allow for multi-factor authentication. With multi-factor authentication enabled, these services require a second form of identification (such as a secondary email address or an authenticator app) before they allow you to log in. In other words, if hackers manage to compromise your email or password, they still won’t be able to access your accounts and distribute malware.
- Keep your system software up to date — When developers find vulnerabilities in their software being exploited by hackers, they patch those vulnerabilities and send the patches to users in the form of software updates. However, with the number of devices, apps, and programs that most users are running these days, it can be tough to keep track of which programs need to be updated. One great tool to do this for you comes from the antivirus provider Avira — it lets you scan your PC for out-of-date software and automatically update it.
- Download parental control software — If your kids have access to your computer, it’s a good idea to have comprehensive parental control software running. That’s because hackers often hide malware files in programs that claim to give kids advantages in games like Fortnite and Roblox. Decent parental control software like Qustodio will stop your kids from accessing suspicious websites containing these disguised malware files.
- Don’t download from websites you don’t trust — You want to avoid downloading from websites you don’t recognize or trust. The vast majority of malware is delivered with seemingly legitimate software. A good antivirus program like Norton can help block most dangerous websites containing this software, but it’s a good idea to also stay vigilant. For example, if you don’t recognize a website, you should research it first and read reviews before downloading from it.
- Avoid torrenting — Torrenting can come with several issues, but one of the most significant problems is that you risk infecting your computer with malware. Since torrenting is a form of peer-to-peer sharing (P2P), you’re downloading files directly from another user. In other words, it’s super easy to download malware from a shady user who has disguised their malware as a trustworthy file.
- Avoid clicking on suspicious email attachments — Hackers often attach malware to deceptive emails. So if you receive an email from a sender you don’t recognize, don’t click on any attachments in that email. Your antivirus can help recognize malicious attachments by scanning emails and tagging suspicious files, and also by scanning all downloads before they can make changes on your computer. However, being careful when going through your email inbox is still a good idea.
- Secure your wireless networks — Make sure your wireless networks are secure before you go online. You can do this by using a firewall, but you should also ensure your home Wi-Fi connection is password-protected. To do this, you need to check your router settings by visiting 192.168.1.1. Unsecured networks are far more vulnerable since anyone can connect to them.
- Use a top VPN — A top VPN like ExpressVPN masks your IP address behind a virtual one, meaning hackers won’t be able to intercept your data or launch man-in-the-middle attacks against you. This is especially important if you’re using public Wi-Fi networks — such as those in coffee shops — as hackers often monitor those Wi-Fi networks and steal data from anyone who uses them unprotected.
- Use a decent ad blocker to avoid malicious pop-ups — A good ad blocker, like the one included in TotalAV, can stop you from receiving pop-ups that contain malicious file downloads. However, if you’re visiting a lot of shady websites or receiving a larger amount of pop-ups than usual, you might already have a malware infection and should also scan your computer using antivirus software.
- Only use an admin account when you need to — When you’re logged into your computer’s administrator account, malware can install new software (such as additional viruses) and access previously restricted areas of your PC. So if you’re just browsing the web or doing day-to-day work, you don’t need to be logged into your administrator account. Only use your admin account when installing new software or important updates.
- Use common sense — Ultimately, when browsing the internet or using your computer, you must be vigilant. If a website or file seems suspicious, it probably is. Similarly, if a website offers something that sounds too good to be true, it’s probably not a trustworthy offer. If you’re not tech-savvy, always double-check websites by doing your research before visiting or downloading from them, and make sure you’re running a comprehensive antivirus program like Norton before you do anything online.
Frequently Asked Questions
Can I disable COM Surrogate?
You can’t disable COM Surrogate. It’s a core system function within Windows that will be called upon every time an application requests it. In order to verify this, I launched Task Manager on my laptop and chose End Task for every occurrence of COM Surrogate. Afterwards, I accessed a folder in File Explorer and opted for Thumbnail View. Upon doing so, I noticed COM Surrogate reappeared in my task list.
This is normal, and it shouldn’t be interfered with. COM Surrogate is a part of dllhost.exe’s function and a required Windows background process. If in doubt, follow this guide on how to remove malicious instances of COM Surrogate.
How do I turn off COM Surrogate?
Unfortunately, it’s impossible to turn off COM Surrogate. Since COM Surrogate is an essential process, even if you force-close it through the Windows Taskbar, Windows will just re-open it the next time it needs it. However, in most cases, there’s nothing to worry about when you see COM Surrogate running. That said, if you’re in doubt, you should check out our instructions on recognizing the malicious version of COM Surrogate and then scan your computer using a comprehensive antivirus scanner such as Norton.
Why does COM Surrogate keep popping up?
If you keep seeing COM Surrogate popping up in your Windows Task Manager, your operating system is calling it to help draw thumbnails or initiate other system commands. COM Surrogate is a form of middleware, so multiple processes within Windows can run it. However, if you’re receiving an actual pop-up that claims it’s COM Surrogate, it’s probably a malware infection. You should scan your computer using an antivirus program such as Norton.
Why does COM Surrogate keep crashing?
It’s totally normal for COM Surrogate to crash occasionally. COM Surrogate is a sacrificial process. In fact, surrogate means to “act in another’s place”. For example, when you open a folder and switch to Thumbnail View, Windows fires a COM Surrogate to draw those thumbnails within File Explorer. If, for whatever reason, this process crashes, instead of having the entirety of File Explorer crash, only COM Surrogate will crash.
In other words, COM Surrogate crashing is a form of protection. That being said, consistent crashes or system slow-downs may be the symptom of something more serious. Should COM Surrogate crash frequently, follow the above steps. Your computer may be infected.
Where is COM Surrogate located?
COM Surrogate is an internal process that is initiated by dllhost.exe — which is located in your System32 folder*.
COM Surrogate itself isn’t something you can find in your system files. Therefore, if you do come across “COMSurrogate.exe” or anything similar, your computer is probably infected with malware and you should check out the rest of my instructions for how to remove it.
*For the less tech-savvy users, the System32 folder is where Window’s most important .EXE and .DLL files are located. If you were to delete System32, Windows would no longer function.
Why is the COM Surrogate virus dangerous?
The COM Surrogate virus is hazardous as it can create a backdoor into your system. This vulnerability can be exploited by cybercriminals to gain unauthorized access to your computer and steal sensitive information, including:
- Usernames
- Email addresses
- Passwords
- Bank account details
- Credit card information
The hacker might download additional harmful content onto your device via a backdoor. This enables them to dominate your OS and use it in botnets and cryptojacking software. Therefore, it’s crucial to thoroughly remove the COM Surrogate virus and any potential malware that may have infiltrated your machine. If you’re uncertain about virus removal from your PC, continue reading my guide on how to eradicate the COM Surrogate virus.
How do I get rid of COM Surrogate in Windows 11?
If you’re seeing COM Surrogate running in Windows 11, it’s perfectly normal. COM Surrogate is a form of middleware that Windows uses to draw thumbnails, among other processes. However, since COM Surrogate is an essential process your computer relies on that can’t be closed, hackers have been known to disguise malware as COM Surrogate. If your computer is running more slowly than usual, or you experience a lot of pop-up ads all of a sudden, you may have a malicious version of COM Surrogate installed. You should follow our guide on recognizing the malicious version, then install a comprehensive antivirus program like Norton that can scan your Windows 11 machine for malware and remove any it finds — including the malicious files disguised as COM Surrogate.