Intro
The Safety Detectives cybersecurity team, led by Anurag Sen, uncovered a critical data leak affecting the Brazilian Marketplace Integrator platform Hariexpress.com.br.
According to the company’s website, Hariexpress integrates several eCommerce marketplaces into a single platform, allowing traders to organize and automate processes across all of their different online stores.
Hariexpress’ misconfigured ElasticSearch server exposed a huge amount of eCommerce customers’ and platform users’ PII.
The last time we checked Hariexpress’ server to verify its status, it had exposed over 1.75 billion records and 610+ GB of sensitive data. It was probably higher by the time it got secured.
Who Is Hariexpress?
Hariexpress was founded in São Paulo, Brazil. The company integrates numerous processes onto a single platform to improve the efficiency and operational ability of traders with more than one eCommerce store.
Features include store cloning and unified inventory management, not to mention ERP analytics that report on business performance.
Hariexpress has some major partners that integrate their services with the platform. These include Mercado Livre, B2W Digital, Amazon, Shopee, Magalu, tinyERP. Bling!, and Nuvemshop.
Correios is another Hariexpress partner. Correios is Brazil’s national postal service, and Hariexpress’ server has exposed data for this major organization too.
We know Hariexpress owns the server due to numerous references to “Hariexpress” in the server’s name and throughout the content of its logs.
What Was Leaked?
Hariexpress’ ElasticSearch server was left unencrypted without any password protection in place. As a result, it exposed 1.75+ billion records, totaling more than 610 GB of data.
Hariexpress’ unsecured database leaked eCommerce customers’ order details, in addition to forms of consumers’ PII data, including:
- Full names; and account “nicknames” (usernames)
- Email addresses
- Phone Numbers
- Full delivery addresses
- Billing details; including billing addresses and the amount paid for goods
- Images of the delivered goods
The open server also included the PII of vendors, i.e. the Businesses using the Hariexpress platform.
As well as leaking data for eCommerce buyers, exposed order details also leaked specific sets of eCommerce vendors’ (sellers’) data:
- Sellers’ full names; and account “nicknames” (usernames)
- Sellers’ email addresses
- Sellers’ phone numbers
- Sellers’ business/home addresses
- Sellers’ CNPJ numbers; an ID number for Brazilian business
- Sellers’ CPF numbers (tax number)
- Billing details; including unit price and time of sale
There were other records on Hariexpress’ open ElasticSearch that exposed PIIs too:
- Links to invoice images; which included shopper & seller names and addresses
- Internal Username and Encrypted Passwords; for each business’ Hariexpress account
- Order tracking numbers
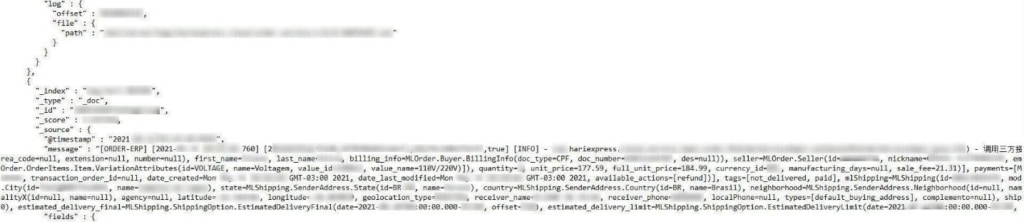
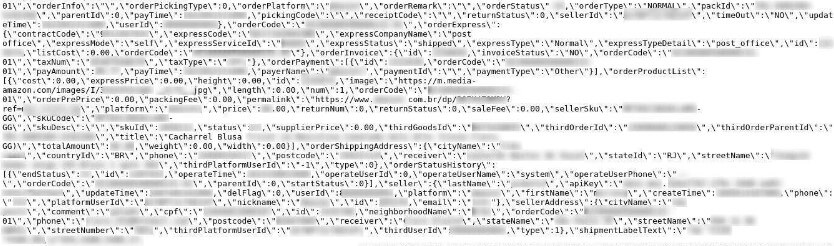
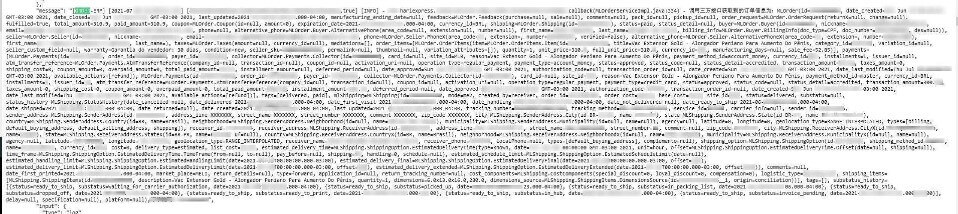
Order details contained a long list of data belonging to eCommerce buyers and sellers. You can see examples of leaked order details below.
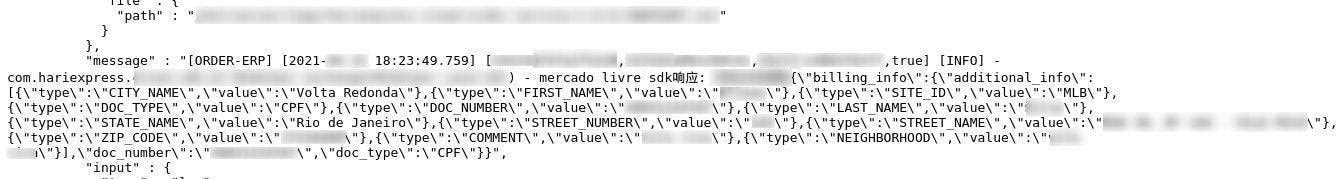
Information including a CPF number
Leaked order details can be an issue in more ways than one. Some logs leak details of eCommerce customers’ sensitive purchases. Orders that were made privately now reveal personal information that one may find embarrassing or damaging.
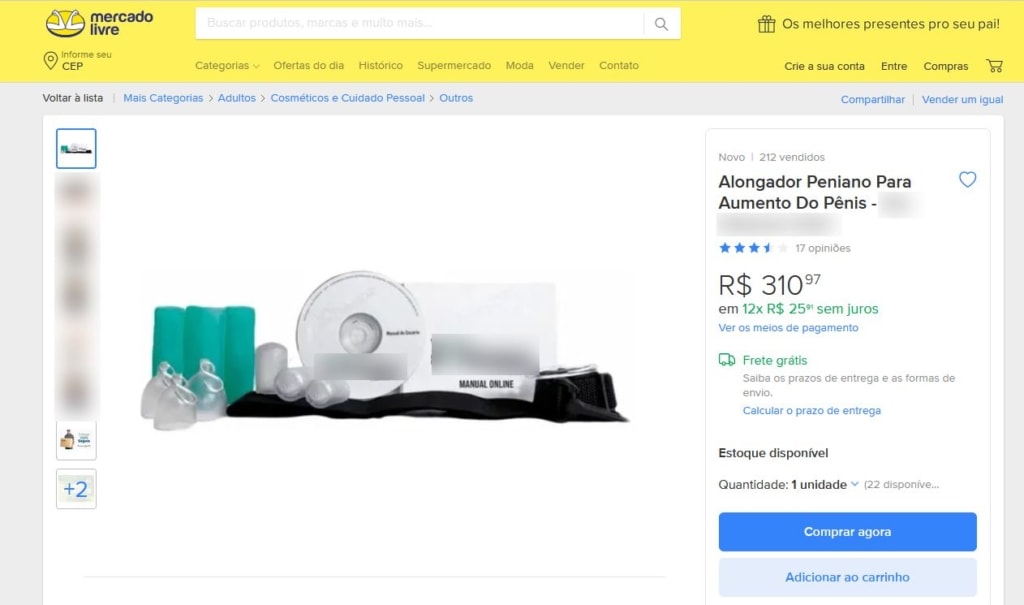
Extensive links to images of the product found in the server
Elsewhere, invoice images and courier service invoices leaked the PII of eCommerce buyers and sellers alike.
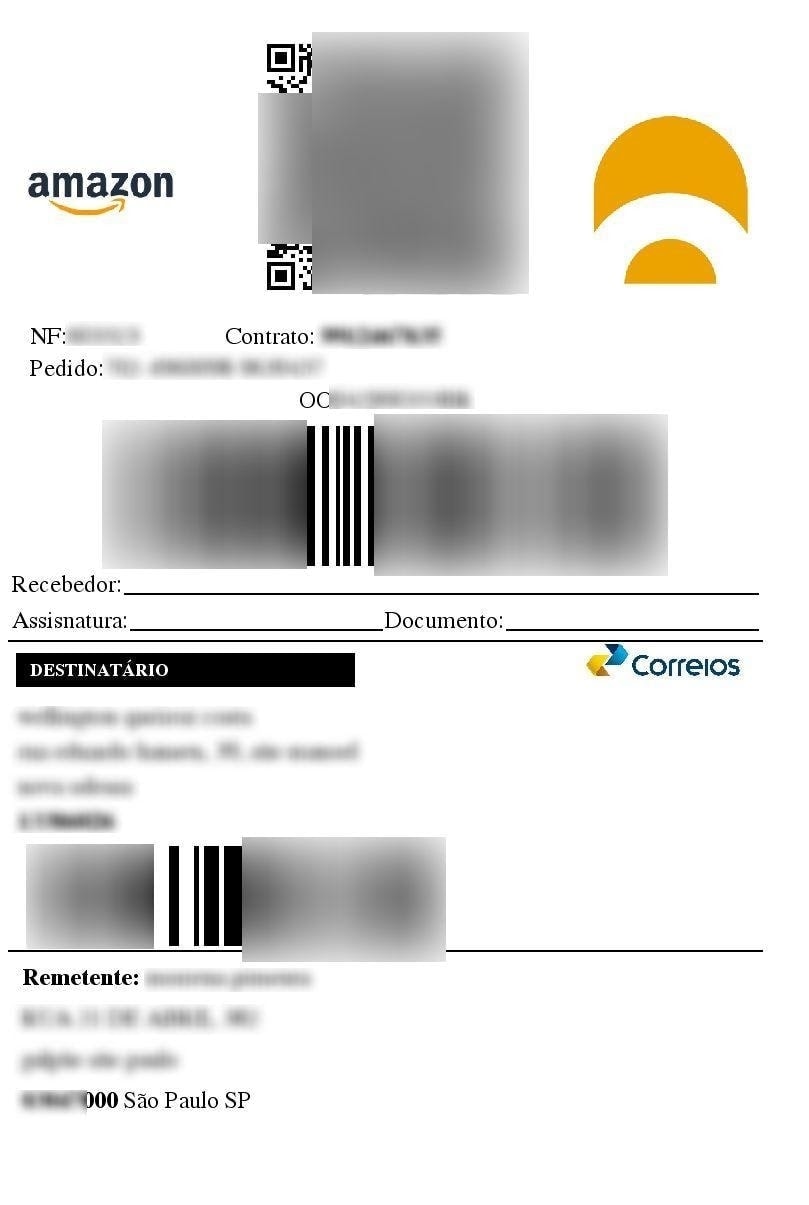
Images of invoices, including delivery invoices
The breach affected eCommerce businesses in other ways, too, with vendors’ Hariexpress account credentials included within the content of the server’s logs. The CNPJ numbers of vendors can also be seen.
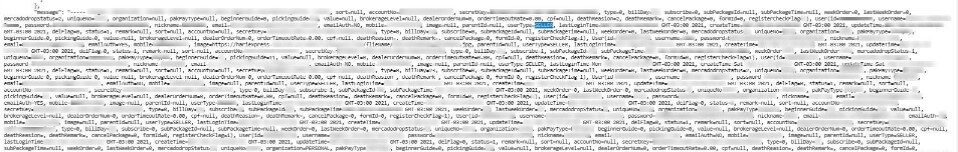

CNPJ numbers
The server’s vast size makes it difficult to know exactly how many people were affected by this breach. We know there were thousands of email address entries on the server’s logs, and as such, we can assume that thousands of people have been affected. However, an exact estimate is difficult due to the presence of duplicate email addresses entries.
You can see a full breakdown of Hariexpress’ data breach in the table below.
Hariexpress’ ElasticSearch server was live and being updated at the time of discovery. The server was apparently exposed on the internet from May 12th, 2021, and the Safety Detectives cybersecurity team discovered it over a month later.
The information in the database was in Portuguese which prolonged our investigation. We reached out to Hariexpress regarding the company’s server on July 1st, 2021, receiving a reply on July 5th, 2021. A Hariexpress employee asked for our contact number but was unreachable thereafter. On July 8th, we contacted Brazilian CERT, who stated they weren’t in charge of such disclosure.
Data Breach Impact
A data breach of this magnitude could easily affect hundreds of thousands, if not millions of Brazilian Hariexpress users and eCommerce shoppers. Hariexpress’ leaked server’s content could also affect its own business.
We cannot know whether unethical hackers have discovered Hariexpress’ unsecured ElasticSearch server. Users, couriers, consumers, and Hariexpress itself should understand the risks they could face from this data breach.
Impacts on eCommerce Buyers
The majority of the server’s critical information belongs to the customers of eCommerce businesses using the Hariexpress platform.
After all, Brazilian eCommerce is a rapidly growing industry, projected to reach 149 billion BRL in 2021. E-commerce platforms may do all they can to safeguard masses of user data but they cannot prepare for a third-party breach like the one covered in this report. This “blind spot” makes mega breaches like the Hariexpress breach possible.
It’s difficult to say exactly how many customers are ultimately affected. If you’re Brazilian and have shopped on any eCommerce platform associated with Hariexpress, then you should be alert to the following cybersecurity threats.
Phishing attacks and social engineering attempts should be at the forefront of any concerned customer’s thinking. Hackers could use leaked email addresses to contact the victim.
Hackers could use a long list of different forms of customer PII to build trust with the victim. The email could be personalized to the recipient using a name and address. The hacker could build a convincing narrative using order information, invoices, and billing details. For example, the hacker could pose as a courier employee, citing an issue with the completion of the order.
From here, the hacker could convince the victim to provide additional forms of personal information or to click a link that downloads malicious software onto the victim’s device. This is a phishing attack.
Phishing attacks can be used to help hackers commit fraud.
Scammers could use CPF numbers to build scams around tax rebates or returns. Scammers could also use invoices and billing information to launch other fraudulent attempts. One such scam is the false billing scam, which uses leaked billing information and invoices to create a fake invoice. The victim then pays this invoice unknowingly.
Theft is another risk to consumers. Criminals could use delivery information and delivery addresses to organize burglary attempts; either of the ordered goods or of the customer’s home address. High-value orders would draw attention to wealthier targets.
Impacts on Hariexpress.com.br Users & Couriers
Hariexpress users and associated couriers are also at risk because of this data breach.
Hariexpress couriers could be on the receiving end of the above-mentioned burglary attempts. Hariexpress integrates a courier service Correios (Brazil’s national postal service) in its platform.
Sellers using Hariexpress must be aware that their names and addresses are included in the open database. Hariexpress users could be targeted with phishing attempts and scams themselves using this information. For example, a hacker could pose as a disgruntled customer to request a refund or new order by citing the extensive list of order logs and invoice information.
Hariexpress users could face account takeover using leaked login credentials. This could be critically damaging for Hariexpress users, providing hackers with a wealth of information about the user’s eCommerce business and customer base.
Corporate espionage is indeed an issue, too. The open ElasticSearch has leaked customer orders for numerous eCommerce businesses. Rival businesses that have acquired this information could contact a seller’s customers, undercutting the original seller with a better offer and stealing that business. This could also be an issue for Hariexpress.com.br.
Rival businesses could also pose as a buyer or colleague, citing customer order details to build trust and find out further information about the seller’s business. This could include industry secrets.
Impact on Hariexpress.com.br
First and foremost, Hariexpress leaked over 1.75 billion records, many of which relate to Hariexpress users and Brazilian members of the public. Hariexpress has placed these individuals in danger of crime, breaking Brazilian data protection laws in the process.
Brazil’s General Data Protection Law (officially Lei Geral de Proteção de Dados or LGPD) came into effect in late 2020. The law applies to any business or person that handles the data of Brazilian citizens.
Businesses that mishandle data will have to pay a maximum fine of 2% of the previous year’s revenue, up to a total of 50 million Brazilian Reals (~$10 million).
Hariexpress could face a loss of business from reputational damage with such a sizable leak. Business owners have entrusted Hariexpress to protect their livelihoods, and Hariexpress has failed to keep this information secure.
Current users may, therefore, look to leave Hariexpress due to cybersecurity concerns. Potential customers could look to use other marketplace integration tools for the very same reason.
Preventing Data Exposure
How can we avoid data exposure and the damaging after-effects of a data leak?
Here are a few tips to prevent data exposure:
- Only provide your personal information to companies/individuals you know, or can completely trust.
- Only visit secure website domains. Secure website domains have a ‘https’ and/or a closed lock symbol at the beginning.
- Be reluctant to provide vendors with the most important forms of personal information (keep government ID numbers and personal preferences to yourself).
- Create rock-solid passwords using letters, numbers, and symbols and update these regularly.
- Don’t click an email link (or any link) unless you are certain the source is legitimate.
- Edit your privacy settings on social media to only show your content and personal information to trusted people.
- Don’t use a credit card or type out account passwords whilst connected to an unsecured Wi-Fi network.
- Learn about cybercrime, data protection, and the ways you can mitigate the risk of phishing attacks and malware.
About us
SafetyDetectives.com is the world’s largest antivirus review website.
The SafetyDetectives research lab is a pro bono service that aims to help the online community defend itself against cyber threats while educating organizations on how to protect their users’ data. The overarching purpose of our web mapping project is to help make the internet a safer place for all users.
Our previous reports have brought multiple high-profile vulnerabilities and data leaks to light, including some 200+ million users exposed by Chinese social media management company Socialarks, as well as a breach that exposed millions of records that implicate users in an Amazon fake reviews scam.
For a full review of SafetyDetectives cybersecurity reporting over the past 3 years, follow SafetyDetectives Cybersecurity Team.